TL;DR
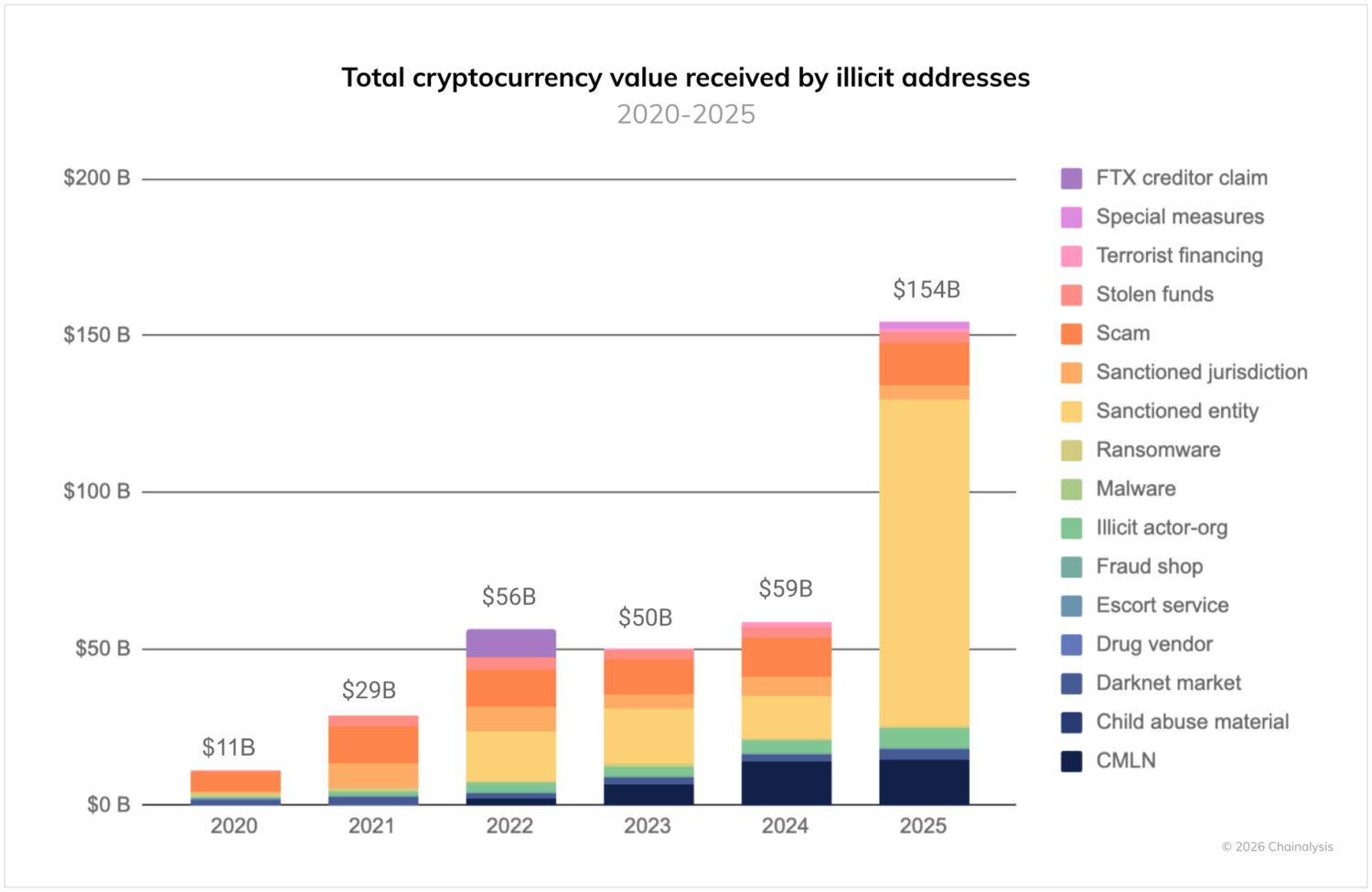
- The value received by sanctioned entities surged 694% in 2025, driving total illicit transaction volume to a record $154 billion as nation-state actors integrated crypto into their national financial infrastructure and strategic policy objectives.
- Iranian crypto activity is increasingly dominated by the state, with the Islamic Revolutionary Guard Corps (IRGC) and its proxy networks accounting for over 50% of value received in Q4 2025, for a total of over $3 billion in transfers throughout the year.
- The ruble-backed A7A5 stablecoin processed $93.3 billion in less than a year, acting as a critical bridge for Russian businesses to access global markets despite sanctions. Grinex and Meer, two exchanges created around the same time as A7A5, were sanctioned in part for facilitating the ruble-backed stablecoin activity and processed at least $4.76 billion and $305 million, respectively, in 2025.
- North Korea stole more than $2 billion in crypto in 2025, making it its most successful year ever. These stolen funds reportedly ultimately end up with the regime to fund their weapons of mass destruction (WMD) program.
- Crypto continued to offer Venezuelans a financial lifeline amid continued hyperinflation and mistrust of the banking system. Despite government attempts to institutionalize crypto domestically, ordinary citizens and regime-affiliated actors have favored access to global exchanges and peer-to-peer (P2P) rails to preserve and transfer value.
- Southeast Asian scam networks have become an increasing area of focus for international regulatory bodies, with sanctions levied against the Prince Group and its CEO, Chen Zhi, for their role in facilitating “pig butchering” scams.
Sanctions evasion has traditionally been viewed as a game of financial shell companies and hidden bank accounts. While those opaque traditional structures remain the bedrock of illicit finance, the mechanism has expanded to the blockchain at scale. Nation-states have upgraded their capabilities not just to launder on-chain, but also to execute cross-border trade. The data support this shift toward large-scale evasion. In 2025, illicit addresses received at least $154 billion, a 162% increase year-over-year. The primary driver of this surge was a 694% increase in value received by sanctioned entities, totaling a staggering $104 billion throughout the year.
At the same time, cryptocurrency’s role in nation-state strategy extends well beyond evasion. States are using blockchain infrastructure for a spectrum of licit and illicit objectives: trade settlement, reserve diversification, procurement of dual-use goods, ransomware enablement, cyber operations, and financial innovation. As we noted in the introduction of our report, crypto adoption continues to expand globally across legitimate and illicit markets, creating a parallel environment in which the same stablecoin rails that facilitate remittances or cross-border commerce can also enable sanctioned trade flows. This convergence can complicate enforcement; the focus is no longer solely on isolating bad actors, but also on identifying when large-scale use of crypto crosses into sanctions violations or national security risk. Against that backdrop, the remainder of this section examines how sanctioned entities — which often include the states that host, fund, and provide them with material support — are operationalizing the blockchain.
In 2025, international regulatory bodies significantly stepped up coordinated sanctions efforts targeting cryptocurrency-related financial activity perceived as facilitating illicit finance and sanctions evasion, with key actions from the U.S. Office of Foreign Assets Control (OFAC), the European Union, the U.K.’s Office of Financial Sanctions Implementation (OFSI), and allied Western nations. OFAC continued to designate crypto actors and infrastructure tied to ransomware, state-linked evasion networks, and sanctions-circumvention services. This illustrates a consistently evolving regulatory approach to blockchain-native illicit activity.
Meanwhile, the EU adopted sweeping sanctions packages, including measures explicitly targeting Russian crypto providers and a ruble-backed stablecoin, A7A5. A7A5 facilitated $93.3 billion in transactions in just 10 months, reflecting the growing use of digital assets to circumvent sanctions and facilitate cross-border trade. These efforts underscore an increasingly multilateral sanctions regime that blends traditional financial controls with blockchain-specific actions to disrupt the use of digital assets for circumventing economic sanctions.
The chart below visualizes this expanding web of enforcement, mapping sanctioning bodies to their specific designations. It highlights the heavy concentration of coordinated actions in the Russia and Cyber sectors, as well as the growing roster of international agencies now actively policing the crypto ecosystem.
In March 2025, OFAC formally delisted decentralized, non-custodial mixer Tornado Cash from its Specially Designated Nationals (SDN) List following a court ruling that its autonomous smart contracts could not be treated as property subject to sanctions, reflecting ongoing legal and regulatory debates about decentralized protocols. Beyond the delisting, national and international authorities remain vigilant about the risks posed by privacy-enhancing tools to obfuscate transactions, which are not inherently illicit, but are often abused by sanctioned and other malign actors.
A diversifying threat: From $2 billion in DPRK hacks to state-backed procurement
In 2025, nation-state use of cryptocurrency moved decisively into the billions. What were once experimental and opportunistic tactics have matured into institutionalized strategies embedded within national economic and security policy. Russia, Iran, and North Korea each operate with distinct objectives and tradecraft, yet despite differing operational models, the three states have collaborated across a number of military, technological, and economic domains in recent years. Collectively, their on-chain behavior demonstrates the same underlying shift: crypto is no longer peripheral to their sanctions evasion, but rather one of its critical elements.
Iran continued integrating crypto into its strategic priorities and financing for proxies, even as the regime faced internal and external pressures not seen since the early days of the Islamic Republic. In Q4 2025, IRGC-linked addresses accounted for over half of all value received by Iranian entities, moving more than $3 billion to support regional militia networks, facilitate oil sales, and procure dual-use equipment. Meanwhile, for Russia, once ambivalent about cryptocurrency, legislation passed in 2024 crystallized into operational reality in 2025, as cross-border trade began settling on-chain at industrial scale. The ruble-backed A7A5 stablecoin processed more than $93 billion in less than a year, functioning as a purpose-built settlement rail for sanctioned actors seeking access to the international financial system.
As the most dramatically isolated of this group from the international community, North Korea remains as aggressive and sophisticated as ever. In 2025 alone, DPRK-linked actors stole over $2 billion in cryptocurrency while continuing to embed IT workers globally to generate revenue for the Kim regime. In addition, many categories of illicit on-chain activity, from money laundering networks to OTC brokers to infrastructure providers, increasingly intersect with actors operating in or connected to China, which maintains economic, diplomatic, and military relationships with all three states. Taken together, these examples illustrate a diversifying threat landscape where on-chain activity serves as a strategic instrument of state power.
Iran’s $3 billion+ proxy network
In Iran, the integration of cryptocurrency into state strategy grew in 2025. In 2026, Iran stands as a primary example of how geopolitical upheaval and economic pressure can drive expanded crypto use both as a tool to safeguard economic activity and as a parallel financial system, with its multibillion-dollar on-chain ecosystem reacting to domestic unrest and external military attacks against it in near real-time. The Iranian crypto ecosystem reached over $7.78 billion in 2025, growing amid domestic instability and external military pressure. From nearly 75 identified mainstream cryptocurrency exchanges in Iran, to the Islamic Revolutionary Guard Corps (IRGC) use of crypto, to leaked data around the Central Bank of Iran’s use of crypto, it is clear that crypto — and more specifically stablecoins — are top of mind for the financial operations of the regime and Iranians writ large.
The IRGC’s 50% market share
Addresses associated with IRGC facilitation networks rose steadily throughout the year, accounting for over 50% of the total value received by Iranian services by Q4 of 2025. In 2025 alone, the volume of funds received by these IRGC-associated addresses spiked to more than $3 billion (up from $2 billion the previous year). Crucially, this $3 billion total is a lower-bound estimate that excludes volumes from major entities like the UK-registered exchanges Zedcex and Zedxion, as these services were not designated until January 2026. When OFAC finally sanctioned these platforms for facilitating transactions on behalf of IRGC-linked networks, it revealed they had processed tens of billions of dollars’ worth of transactions tied to Iran-aligned actors, highlighting how exchange infrastructure can serve as critical nodes in state-backed crypto activity.
In February 2026, the US and Israel launched coordinated military strikes on Iran that targeted defense infrastructure and strategic leadership, and killed the Supreme Leader. Crypto markets responded with visible on-chain asset movements in near real time. Our data can capture the dynamic ebbs and flows of wallet activity of Iranian exchange counterparties, illustrating that major geopolitical events often manifest quickly on public ledgers and provide useful analytic indicators.
Beyond the immediate market reaction to conflict, however, a primary objective of this state-sponsored financial architecture remains the sustained support of external operations. These funds are used to finance a web of regional militia proxies, including Lebanese Hezbollah, Hamas, and the Houthis, facilitating the movement of commodities, illicit oil, and arms at scales not seen on the blockchain before.
Crucially, blockchain data have become a barometer for kinetic conflict. We observed significant spikes in Iranian on-chain volume corresponding directly to major geopolitical events, including the Kerman bombings, missile strikes in October 2024, and the 12-day war in June 2025. In the same month, cyberattacks targeted Nobitex, Iran’s largest exchange, draining its reserves for over $90 million; however, the exchange has largely recovered since.
Central Bank of Iran: A shift to the blockchain
In late 2025 Iranian businessman and OFAC SDN Babak Morteza Zanjani – who was initially listed as Zedxion’s director in 2021 – posted leaked documents with addresses belonging to the Central Bank of Iran in a social media post. The documents indicated that the regime was using a broker to facilitate the purchase of stablecoins from fiat currency deposits, unraveling a network of coordinated central bank laundering that is unprecedented in its organization and scale.

Blockchain analysis reveals that the broker hired by the regime to purchase stablecoins has exposure to other regime proxies, including Iranian national and OFAC SDN Alireza Derakhshan, who coordinated the purchase of over $100 million worth of cryptocurrency related to Iranian oil sales between 2023 and 2025. Further, the analysis demonstrates how regime actors laundered the central bank funds through several bridges and DeFi protocols before moving the funds back into the mainstream Iranian crypto ecosystem and IRGC-affiliated entities.

This analysis underscores the extent to which nation states like Iran, subject to heavy sanctions prohibiting the movement of fiat funds, have turned to crypto to facilitate foreign trade activities and have skillfully learned how to obfuscate their activity on the blockchain. Notably, blockchain analysis has evolved to track this activity in real-time.
Bitcoin as protest: The civilian flight to self-custody
While the state uses crypto for warfare, Iranian citizens have used it for survival. Facing inflation rates of 40-50% and a collapsing rial, civilians have turned to cryptocurrency as an alternative mechanism.
Comparing the pre-protest window (Nov–Dec 2025) to the period of the internet blackout (Jan 2026), we observed a surge in withdrawals from Iranian exchanges to personal Bitcoin wallets. Unlike the state, which favors stablecoins for settlement, civilians are taking possession of bitcoin at markedly higher rates. This “flight to self-custody” indicates that for the average Iranian, bitcoin has become a censorship-resistant asset that offers financial flexibility in an authoritarian and highly volatile environment.
The $93 billion bridge: How A7A5 industrialized Russian sanctions evasion
A prime example of the landscape’s complexity is the role of the A7A5 token network. In August 2025, OFAC and OFSI designated entities tied to A7A5, a Russian ruble-backed token, along with its affiliated exchange Grinex and Kyrgyzstani issuer Old Vector. This was followed by the European Commission’s 19th sanctions package in October 2025, which enacted a transaction ban on A7A5 itself and the tokens’ related entities.
A7A5 represents an evolutionary step in sanctions evasion: a token expressly designed to bypass the traditional financial system entirely. Our on-chain analysis reveals several critical features of this network:
- Grinex is the direct successor to Garantex, the notorious Russian exchange sanctioned in 2022 that has processed hundreds of millions of dollars’ worth of illicit transactions. Following the disruption of Garantex’s online infrastructure in March 2025, on-chain data showed a massive transfer of user funds and newly minted A7A5 tokens moving directly from Garantex wallets to Grinex via Old Vector. This was a clear “rebranding” effort to maintain liquidity for sanctioned entities.
- Unlike retail tokens, A7A5 trading volumes surge Monday through Friday and drop precipitously on weekends. This pattern suggests the token is being used primarily as a settlement layer for the Russian government and businesses to settle cross-border accounts during business hours, rather than for retail use which typically operates 24/7.
- Perhaps most concerning is the A7A5 Instant Swapper service. This instant exchange service operates without meaningful or no KYC, and converts the sanctioned A7A5 token into mainstream USD‑pegged stablecoins. To date, over $2.2 billion in value has moved through this service, effectively allowing sanctioned Russian entities to transfer assets from sanctioned Russian banks, through a now sanctioned ruble-backed stablecoin into the broader global crypto economy, in an effort to allow the ability to facilitate cross-border trade outside of the traditional fiat ecosystem.
- Dozens of addresses with high activity within the A7A5 network belonging to sanctioned Moldovan oligarch Ilan Shor were leaked in 2025, revealing key sources of liquidity for the A7A5 Instant Swapper. Prior to the joint law enforcement takedown of Garantex in March 2025, Shor representatives met with Garantex administrators to set up A7A5 trading.
Russia’s use of A7A5 illustrates not only how sanctioned states are building parallel financial rails, but also how enforcement authorities are adapting in response. Sanctions against entities like bulletproof hosting providers Zservers, AEZA, and Yalishanda and IP infrastructure provider Funnull Technology demonstrate a growing regulatory focus on the infrastructure layer that enables on-chain illicit activity. Authorities are no longer just targeting the wallets receiving illicit funds; they are dismantling the Infrastructure as a Service (IaaS) providers that allow state-sponsored hackers and ransomware gangs to operate. This “infrastructure-centric” approach aims to disrupt the operational capacity of sanctioned entities at its foundation – restricting hosting services, liquidity pathways, and technical backbones that keep networks online. By targeting these service providers, regulators increase costs, fragment ecosystems, and force sanctioned actors to rebuild in less stable and more exposed environments.
From survival to statecraft: Cryptocurrency’s split reality in Venezuela
Venezuelan nationals were early adopters of crypto, using it as a hedge against hyperinflation, and sustained instability in the domestic banking sector under the Maduro regime. In 2025, we identified an estimated $44.6B in transaction flows in Venezuela. While the Government of Venezuela (GoV) sought to formalize and oversee the sector through the creation of Superintendencia Nacional de Criptoactivos (SUNACRIP) and a network of state-run exchanges — including support for the now-defunct state-backed crypto asset, the Petro — Venezuelans instead flocked to international cryptocurrency exchanges, in large part reflecting limited confidence in the regime’s offerings. The state-run exchanges ultimately had limited success, conducting transactions totaling in the tens of millions until their eventual shut down, a far cry from broad adoption. As the sanctions targeted the GoV rather than ordinary citizens, many global exchanges permitted Venezuelan nationals on their platforms, creating a critical financial lifeline to the global financial system amid domestic constraints.
At the same time, informal networks, potentially linked to the regime, operate alongside mainstream usage. Beyond the formalized ecosystem under SUNACRIP, reports indicate the Maduro regime has engaged in stablecoin-for-oil trade. These typologies suggest these regime-aligned financier networks may mirror models observed in other sanctioned jurisdictions, such as Iran and Russia, facilitating cross-border trade and evading sanctions all at once.
Furthermore, informal over-the-counter (OTC) brokers, whether operating physical storefronts or offering services tailored to Venezuelan nationals, continue to function as on- and off-ramps. Certain brokers have enabled swaps into crypto from bolivars held at sanctioned Venezuelan banks.
In one example (depicted below), an OTC broker shows direct on-chain exposure to Chinese-language money laundering networks (CMLNs) and the recently FinCEN 311-designated Huione Group. Such exposure underscores the risk that these intermediaries may facilitate the laundering of illicit proceeds, whether related to state-linked actors, transnational organized crime, or unrelated independent actors. These services therefore represent informal, largely unregistered conduits between Venezuela’s highly turbulent domestic financial system and the global crypto ecosystem.
Overall, Venezuela’s relationship to cryptocurrency reflects a dual dynamic. For individual citizens, crypto primarily provides access to global exchanges and a mechanism to preserve value amid persistent macroeconomic volatility. For the GoV, attempts at institutionalizing and controlling domestic adoption have largely failed; however, the strategic use of crypto by the regime to facilitate cross-border trade and evade sanctions, especially in the oil sector, has found success. This tension highlights the dynamic push and pull we observe in heavily sanctioned environments: crypto can simultaneously function as an instrument of state-level sanctions evasion and as a stabilizing financial outlet for beleaguered populations navigating prolonged economic distress and illicit finance risk. While Venezuela’s crypto ecosystem continues to reflect the interplay between economic hardship and sanctions pressure, global enforcement efforts have also intensified against other complex networks that leverage crypto to facilitate fraud and laundering at scale.
Regulatory bodies target Southeast Asian scam networks
2025 also saw coordinated actions by U.S. and allied authorities against crypto-enabled scam and laundering networks in Southeast Asia. In October 2025, the designation of Huione Group under FinCEN’s Special Measures as a primary money laundering concern under Section 311 of the USA PATRIOT Act highlighted in particular how cross-border enforcement is adapting to confront highly automated, high-volume on-chain illicit activity. Huione Group has processed over $98 billion of total cryptocurrency inflows between August 2021 and January 2025, including over $4 billion in confirmed illicit proceeds. Huione Group has long been used by a host of illicit actors, ranging from money launderers, scam technology vendors, escort services, and more. Along with Huione’s designation, the transnational criminal organizations Prince Group and its frontman Chen Zhi were targeted with sanctions in multiple jurisdictions for their role in facilitating cryptocurrency scams, mining operations, money laundering, and forced labor at scam compounds in Cambodia and beyond. Additionally, OFAC designated Jin Bei, a guarantee platform facilitating activity similar to Huione Group, and OFSI also sanctioned Byex, a cryptocurrency exchange platform with links to Prince Group. Over $15 billion of Chen Zhi’s money was seized by the U.S. government, a landmark disruption; however, following his designation, addresses affiliated with and controlled by Chen Zhi continued to launder his remaining stored value on-chain prior to his arrest in Cambodia and extradition to China in January, as shown in the graph below:
Looking ahead
Sanctions evasion involving cryptocurrency is likely to remain concentrated in a relatively small number of highly capable state actors and their transnational facilitation networks. As we have shown throughout 2025 — from designations tied to A7A5 and Grinex to actions against infrastructure providers like Zservers and AEZA — enforcement is increasingly focused on the service layer that enables illicit activity, not just individual wallets. It is also important to remember that the billions of dollars attributed to IRGC-linked wallets, DPRK hacking groups, and other state actors ultimately move through networks of individual brokers, facilitators, IT workers, and other operators whose activity in the aggregate gives state-backed campaigns their breadth and depth. Even at billion-dollar volumes, these ecosystems are run by human beings making operational decisions, leaving behavioral patterns and infrastructure dependencies that can be traced and disrupted. Targeting exchanges, hosting providers, OTC brokers and other facilitators can thus have outsized impact by disrupting liquidity and operational continuity for complex, multi-jurisdictional sanctioned networks.
At the same time, sanctioned actors are likely to continue to rely on stablecoins and centralized services, because they offer the liquidity, global presence, and interoperability needed for cross-border trade. While tactics such as chain-hopping and rapid rebranding (e.g., Garantex-to-Grinex) are likely to persist, the blockchain’s transparency will remain a structural advantage for investigators, compliance teams, regulators, and policymakers. 2025 provided clear examples across a range of geopolitical challenges that real world risk manifests on-chain, with observable changes in trading patterns and large-scale flows, as regimes and the citizens living under their yoke responded to heightened uncertainty. This underscores the utility of our data not only for tracking illicit finance, but also for providing real-time insight into how macro developments influence risk sentiment across digital asset markets. Stronger analytics, more comprehensive data, closer public-private collaboration, and coordinated designations have made large-scale evasion more visible — even when it is moving at a billion-dollar scale.
Looking to the longer-term, as economies such as Venezuela and Iran eventually confront the prospect of reconstruction and reintegration into the international system, crypto and on-chain infrastructure could play an important role in rebuilding trust in repairing badly damaged financial systems and expanding access to basic services. Stablecoins and on-chain settlement mechanisms in particular offer low-cost, borderless avenues for remittances, payments, and savings for populations underserved by the formal banking sector and plagued by corruption, opaqueness, and AML/CFT risk. If coupled with sound regulation and inclusive policy frameworks, these tools could help governments leverage crypto not just for resilience, but also for broader financial inclusion as part of economic recovery.
This website contains links to third-party sites that are not under the control of Chainalysis, Inc. or its affiliates (collectively “Chainalysis”). Access to such information does not imply association with, endorsement of, approval of, or recommendation by Chainalysis of the site or its operators, and Chainalysis is not responsible for the products, services, or other content hosted therein.
This material is for informational purposes only, and is not intended to provide legal, tax, financial, or investment advice. Recipients should consult their own advisors before making these types of decisions. Chainalysis has no responsibility or liability for any decision made or any other acts or omissions in connection with Recipient’s use of this material.
Chainalysis does not guarantee or warrant the accuracy, completeness, timeliness, suitability or validity of the information in this report and will not be responsible for any claim attributable to errors, omissions, or other inaccuracies of any part of such material.