TL;DR
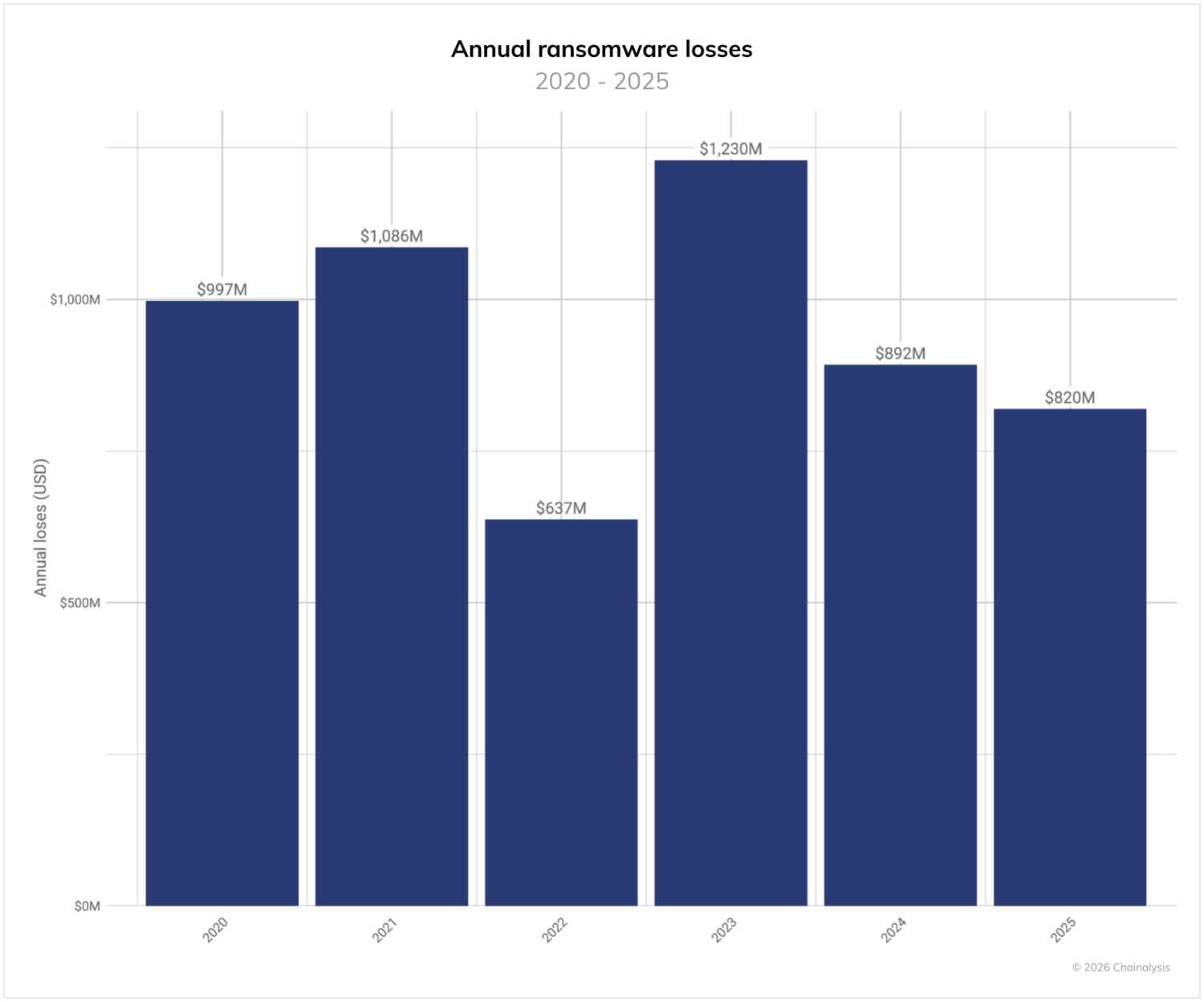
- Ransomware payments stagnated despite record attacks claimed. Total on-chain ransomware payments fell by approximately 8% to $820 million in 2025, even as claimed attacks rose 50%.
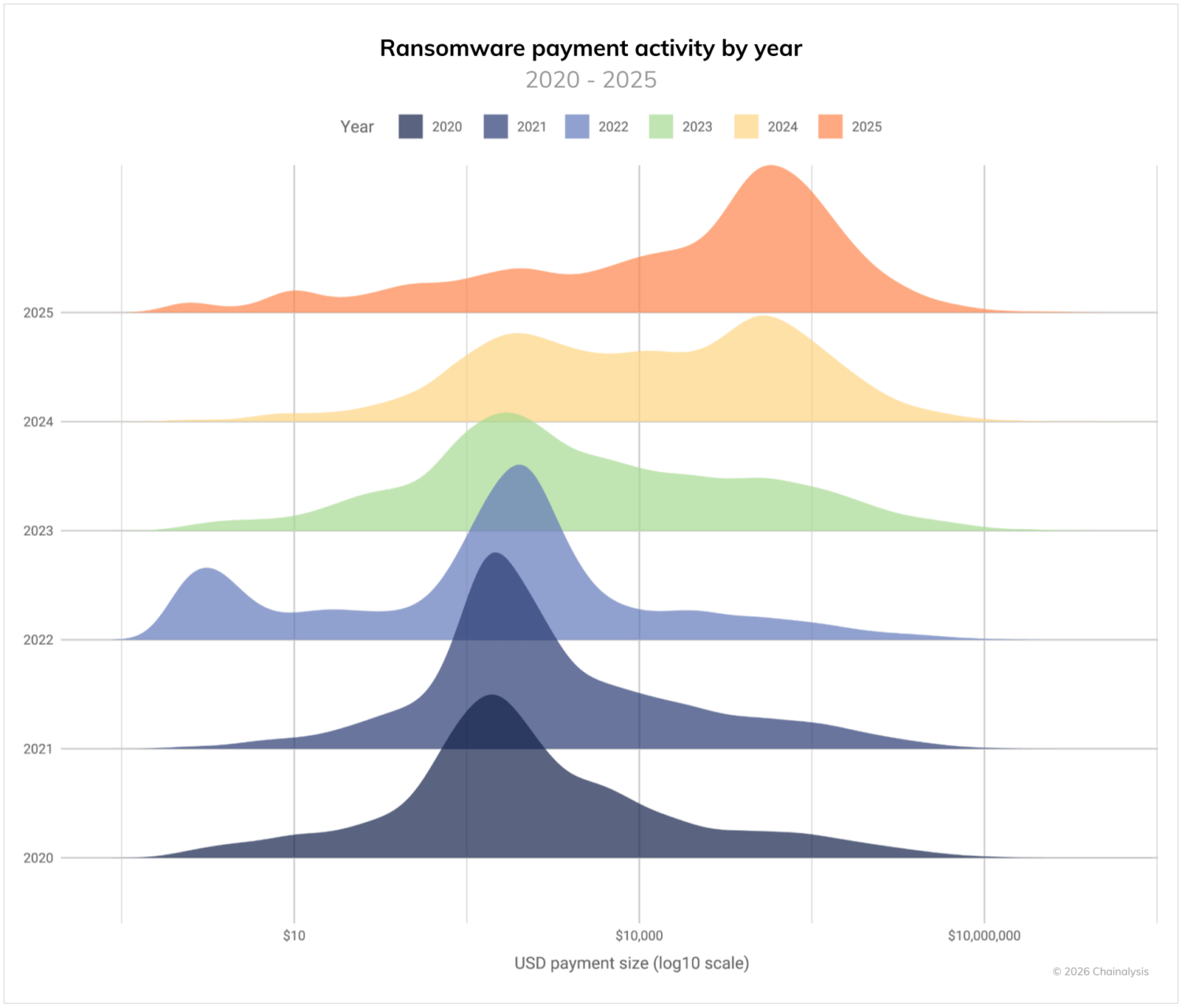
- Median ransom payment size increased significantly. While aggregate revenue stagnated, the median ransom payment grew 368% year-over-year to nearly $60,000.
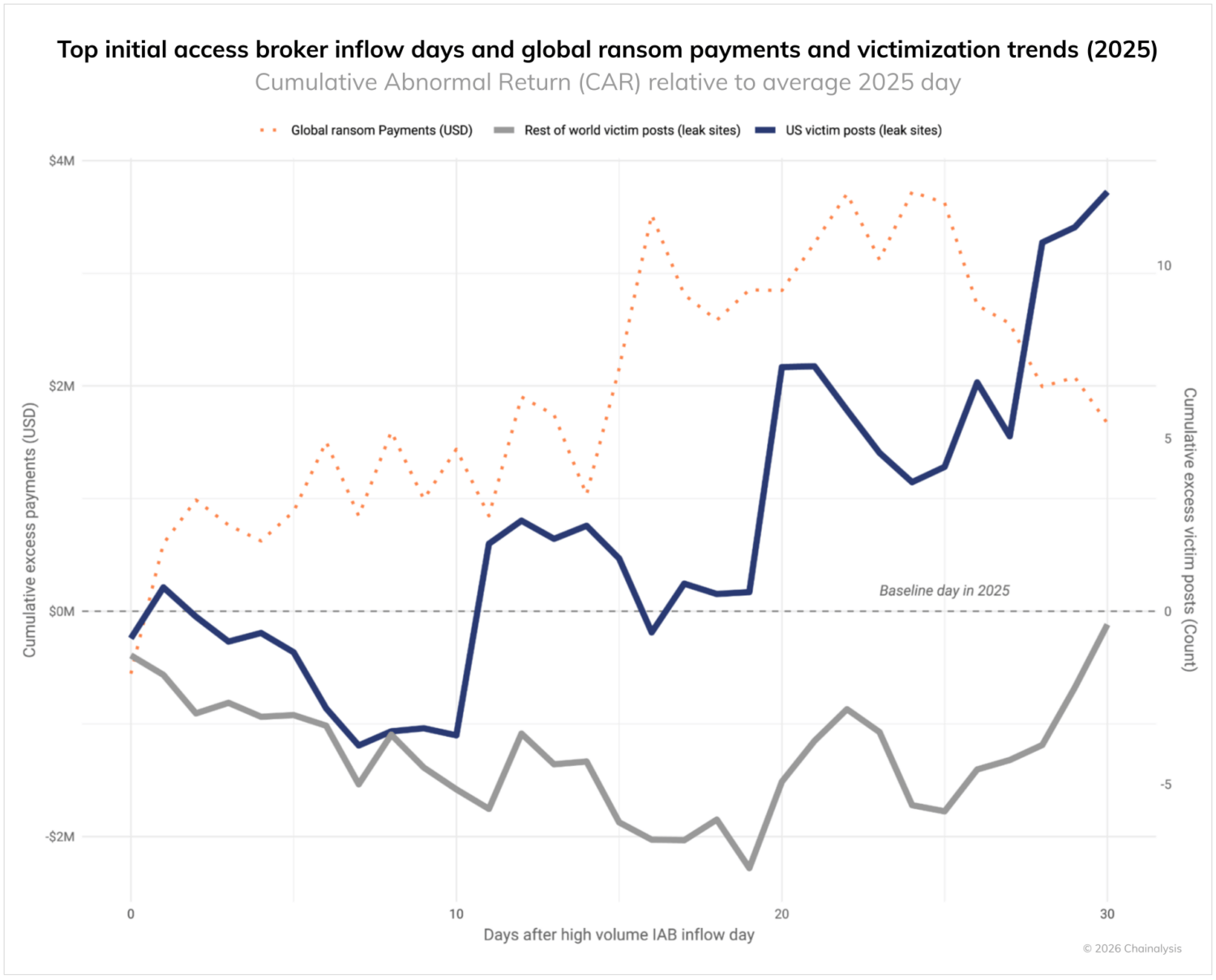
- Initial Access Broker (IAB) activity can serve as a leading indicator; on-chain analysis indicates that spikes in IAB inflows typically precede increases in ransomware payments and victim leaks by roughly 30 days.
- Criminal and state-linked actors share infrastructure. The infrastructure layer has converged, with financially-motivated cybercriminals and state-aligned actors using the same bulletproof hosting providers and residential proxy networks to evade detection.
- Disruption efforts focused on the enablement layer. Law enforcement actions and sanctions, as well as private sector efforts, in 2025 increasingly targeted infrastructure services in addition to individual groups, aiming to disrupt the hosting and malware loading tools used across the ecosystem.
Ransomware today is best understood not as isolated attacks, but rather as an interconnected marketplace of access, infrastructure, and monetization services. In 2025, total on-chain payments remained relatively stagnant even as claimed attacks increased and median ransom sizes rose. At the same time, coordinated law enforcement actions and sanctions increasingly targeted the infrastructure layer — including bulletproof hosting providers — increasing costs across both cybercrime syndicates and state-linked actors.
In 2025, ransomware actors received more than $820 million in on-chain payments — an 8% decline year-over-year (YoY) from $892 million, our updated 2024 estimate. The 2025 total is likely to approach or exceed $900 million as we attribute more events and payments, just as our 2024 total grew from our initial $813 million estimate this time last year.
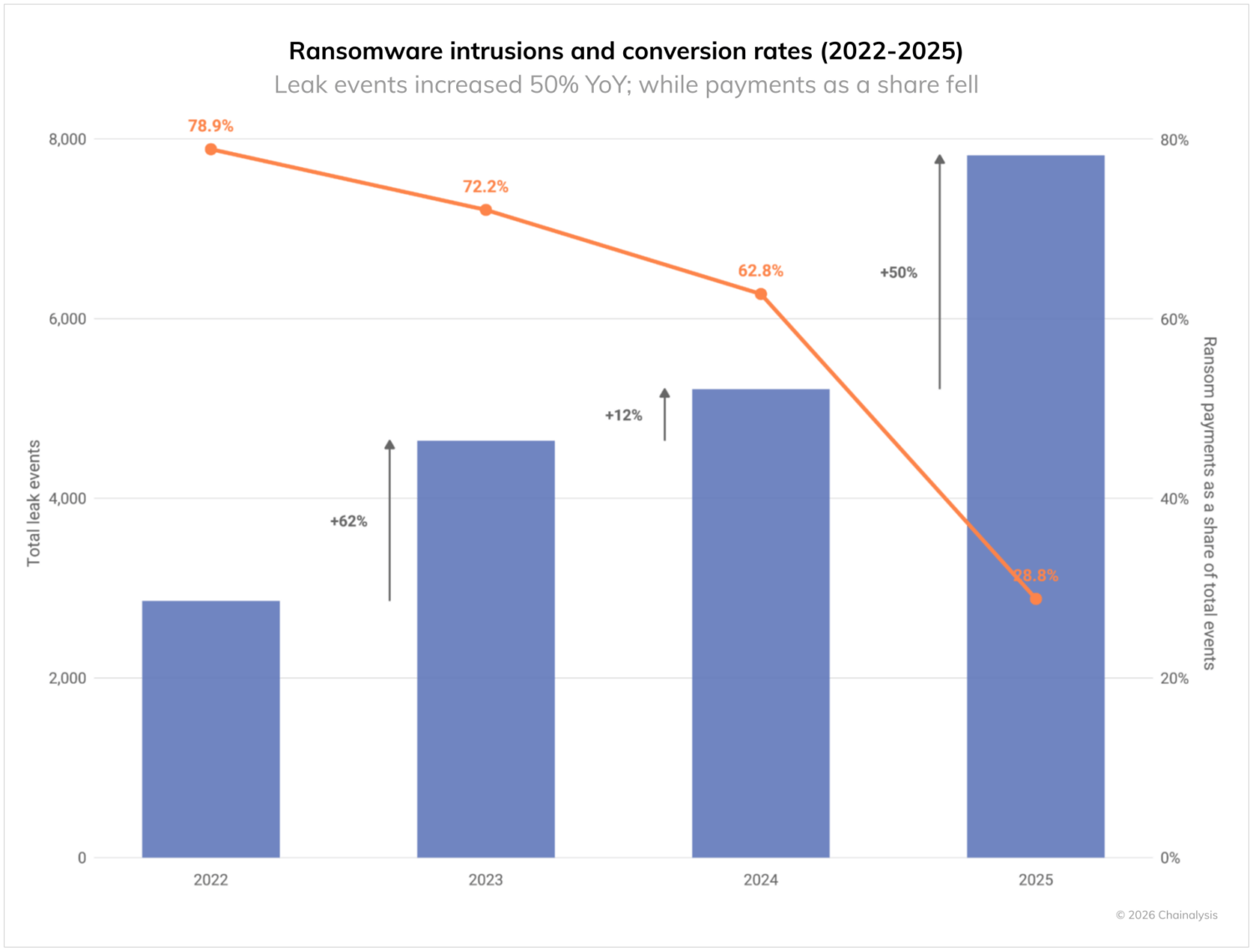
Despite the relative stability in total payments, ransomware attacks surged across multiple vectors in 2025, with eCrime.ch data showing a 50% YoY increase in claimed ransomware victims, marking the most active year on record. Thanks to this dynamic, the share of ransoms paid potentially reached an all-time low this year at 28%.
This divergence — more claimed attacks, but fewer aggregate payments — reflects complex forces shaping the ransomware economy:
- Improved incident response and increased regulatory scrutiny have helped reduce payout frequency.
- Effective international action against ransomware operators, infrastructure, and laundering networks has constrained some revenue flows.
- In some cases, the introduction of strains like VolkLocker, notable for a cryptographic weakness that allowed free decryption in some cases, illustrates how technical vetting by defenders can occasionally disrupt a ransomware strain.
- Marked fragmentation of major ransomware-as-a-service (RaaS) operations and decreasing centralization in the ransomware market have led to a proliferation of smaller, independent ransomware actors, with some analyses tracking as many as 85 active extortion groups.
The shift from a large handful of dominant strains to a more decentralized and volatile landscape has made attribution, response, and long-term tracking as important as ever. According to the founder of eCrime.ch, Corsin Camichel, “We’re seeing a structural shift in targeting: fewer large, headline-grabbing intrusions and more volume focused on small and medium enterprises. The assumption is simple — smaller victims pay faster. However, Chainalysis’ data shows payments trending downward despite an all-time high in public claims. That divergence is important. It suggests attackers are working harder for diminishing returns.”
This overall trend is a major win against the ransomware ecosystem. Fewer victim payments mean more work for less for attackers, an important step in shifting the economic incentives.
Median ransom payments and shifting extortion tactics
While total payments flatlined, media n payment sizes increased significantly in 2025. In particular, the median payment increased 368%, from $12,738 in 2024 to $59,556 in 2025. This dynamic mirrors reports from incident response firms that median payouts more than doubled in certain quarters.
High-impact incidents shaped the ransomware landscape
Several widely publicized trends – from zero-day exploits to social engineering – made 2025 another devastating year for ransomware’s global scale and impact:
- One of 2025’s most economically disruptive cyber events was the cyberattack on Jaguar Land Rover, which halted production lines across multiple countries and inflicted an estimated £1.9 billion (approximately $2.5 billion) in economic damage, the costliest cyber event in UK history.
- Retail and services sectors also felt ransomware’s impact. Major British multinational retailer Marks & Spencer grappled with prolonged disruption after a breach by the Scattered Spider ransomware group forced extended operational outages and wiped hundreds of millions of pounds of market value.
- Healthcare providers remained lucrative targets. For example, kidney dialysis company DaVita Inc. experienced one of the most serious healthcare ransomware breaches, resulting in the exposure of almost 2.7 million patient records and substantial loss of allegedly 1.5 TB of clinical data.
Beyond individual companies, mass exploitation events continued to illustrate ransomware’s reach. For example, Cl0p leveraged a zero-day exploit in Oracle E-Business Suite to orchestrate widespread enterprise extortion campaigns that affected hundreds of organizations.
Ransomware actors remain highly opportunistic. They do not consistently favor a specific sector at a given time of year. Instead, they exploit exposed services and misconfigurations as they arise, and capitalize on newly disclosed vulnerabilities.
Fingerprinting strains by financial behavior
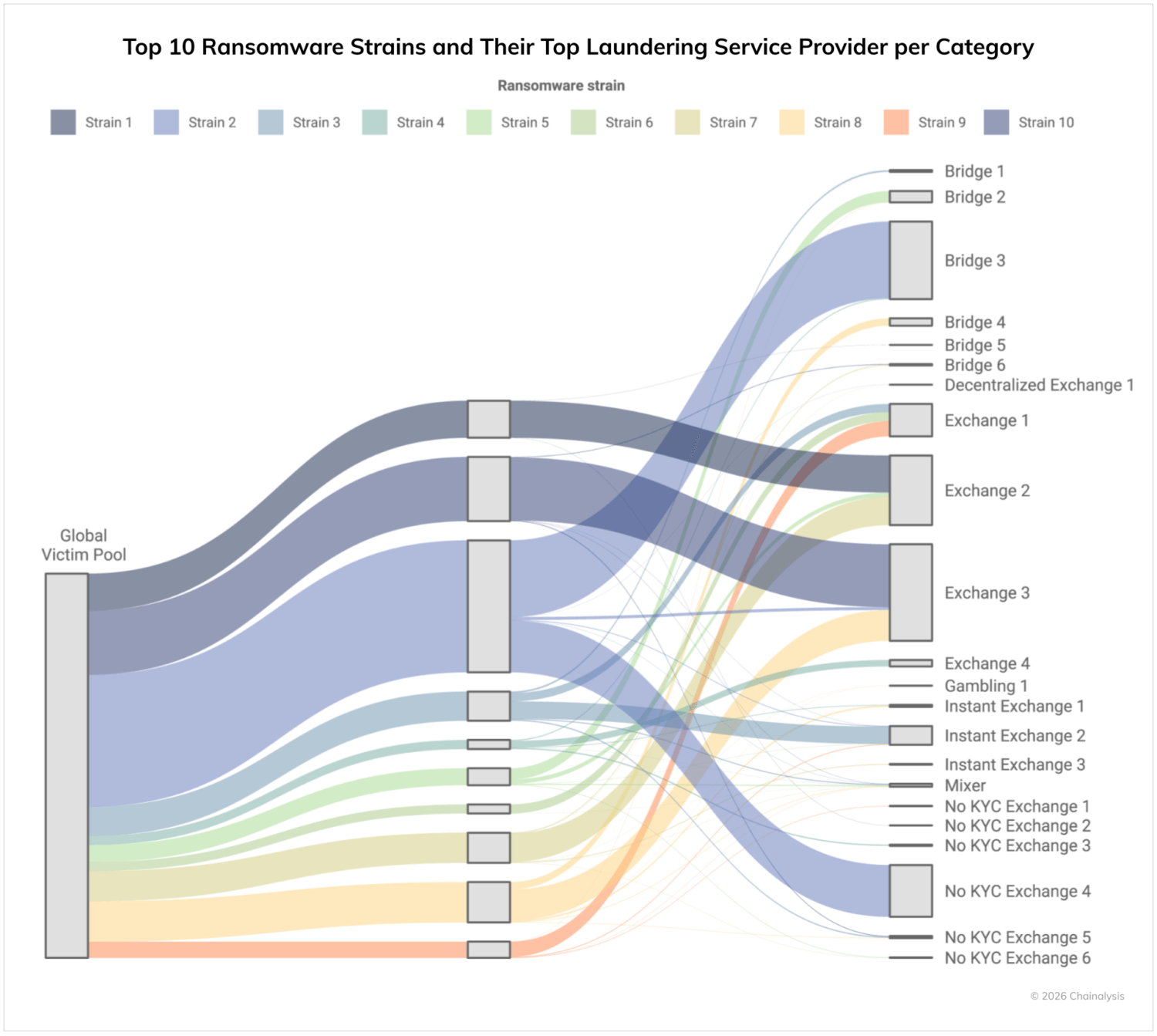
By isolating the primary laundering channels for the top 10 ransomware strains of 2025, we can begin to “fingerprint” these groups based on their distinct on-chain signatures. While the malware they deploy may share code or builders, their exit strategies reveal unique operational preferences.
This divergence across strains allows investigators to distinguish between groups based not only on their attack, extortion, and negotiation TTPs, but also their on-chain behavior. We can also track ransomware actors who work with multiple strains based on their unique laundering patterns.
Leak site activity underscores geographic concentration
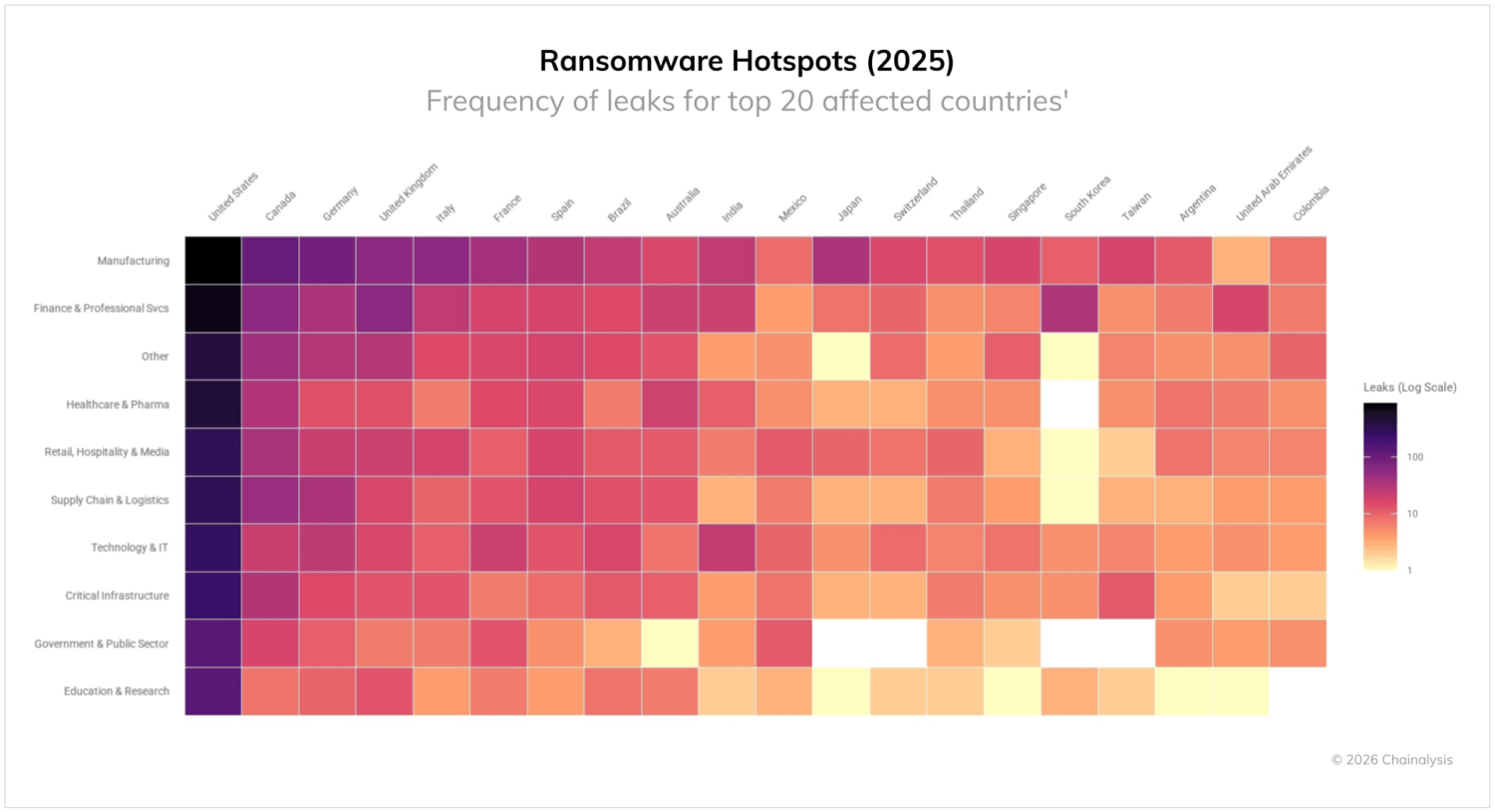
Analysis of leak site disclosures throughout 2025 shows continued disproportionate geographic concentration in developed economies. Data leak site-claimed ransomware incidents grew by 50% YoY — an all-time high.
Among the countries for which there is a clear geographical tag, the United States remains the most heavily targeted jurisdiction, followed by Canada, Germany, the UK, and other parts of Europe. Manufacturing and finance/professional services were the most heavily compromised in most of these jurisdictions, with Canada and Germany having a particularly high compromise rate within supply chains, logistics and critical infrastructure.
One important caveat is that not all data leak site claims are legitimate. Furthermore, data leak site posts may mean that a party has been victimized, but not necessarily that they failed to pay. Incident response firm Arete told us, “This year, we saw several groups reposting old victims or posting victims from other groups’ data leak sites, which skewed data leak site posting rates. However, we continue to see fewer victims making ransom payments as the adoption of security best practices improves, including better backups and the use of security technologies like endpoint detection and response, which disrupt threat groups before they can fully achieve their objectives.”
Arete elaborated that some threat groups responded to this decrease in payments by becoming more aggressive during negotiations, which has included contacting employees and even customers of victimized organizations. Other groups responded by focusing on data exfiltration and even analyzing exfiltrated data to identify what was stolen. By analyzing the exfiltrated data, the threat actors can make more specific threats about the consequences of data exposure.
Not only was the United States hit heavily across sectors; every sector saw increased targeting YoY. Claimed victims from critical infrastructure, supply chains and logistics, and government increased YoY by between 45% and 56%. In other words, the United States is the most targeted nation globally, and the rate of intrusions has increased significantly relative to 2024. Ransomware actors continue to view U.S.-based organizations as high-value and high-liquidity targets.
The ransomware supply chain: initial access brokers (IABs)
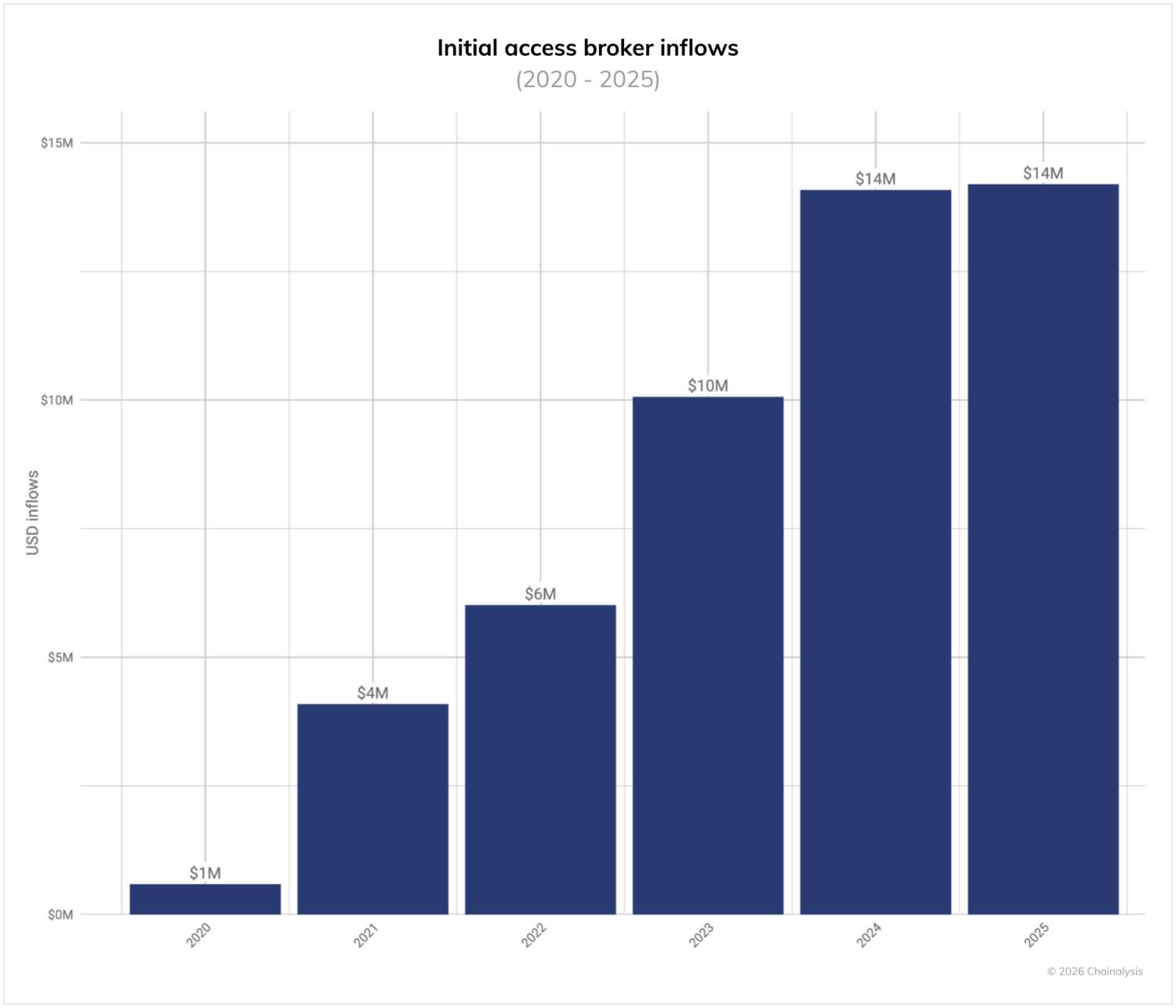
Ransomware does not occur in isolation, but rather is supported by a broader cybercrime supply chain, including Initial Access Brokers (IABs) and other specialized services. As their name suggests, IABs facilitate entry to compromised networks, enabling affiliates to deploy ransomware with relative ease.
The size of this enablement ecosystem is increasing over time. In 2025, we estimate that IABs received at least $14 million in on-chain payments — roughly flat YoY, although we expect this total to grow as attributions improve. Although modest relative to ransomware totals, this figure represents a critical enabling function. Total ransomware payments of approximately $820 million in 2025 represent nearly 58 times the value flowing to IABs, suggesting a substantial return on investment within this segment of the cybercrime supply chain.
It is important to note that not all IAB payments are made by ransomware operators. IABs certainly trade and buy access among themselves and some malicious actors have TTPs and objectives other than ransomware. Another important caveat is that not all ransomware incidents can be traced to IABs — there are a number of different ways to gain access to victim networks. With those caveats in mind, we can draw a connection between criminal investments and the ransomware attacks that follow.
Looking 30-days out from sizable IAB payment inflow events (days within 2025 in the top 25% of all days), we see a significant effect on both global ransomware payments and claimed US victims totals as measured by leak site posts. The chart below plots the cumulative abnormal returns relative to the average day in 2025, and shows an almost immediate and sizable growth in abnormal global ransomware payments (more payments than expected). And, after around a 10-day lull, a similar growth in leak site posts about US victims.
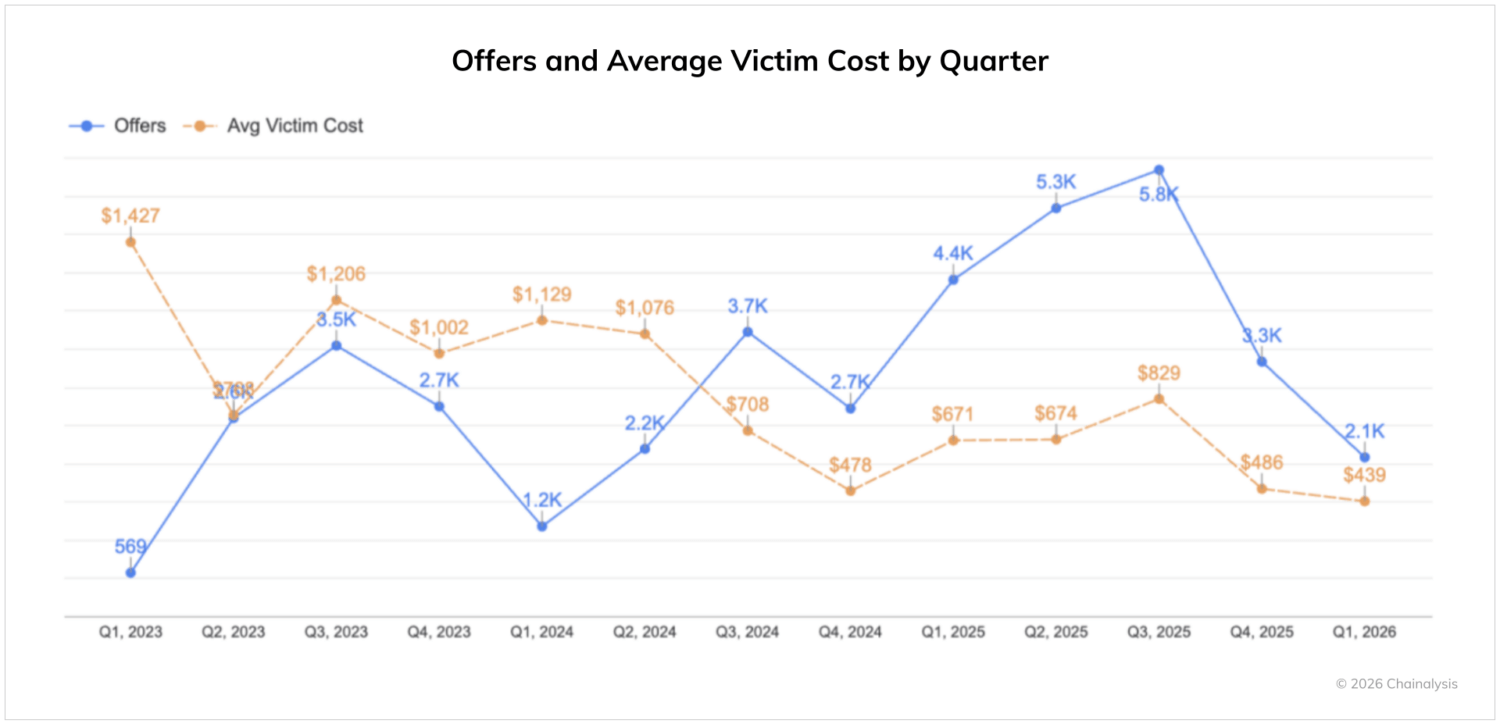
Cybercrime prevention firm Darkweb IQ told us that, from Q1 2023 to Q1 2026, the average price for victim access declined from approximately $1,427 to $439. This drop reflects a market characterized by more competitive pressure and automation as the core shaping force. “We are seeing industrialized access pipelines, AI-assisted tooling, and a proliferation of infostealer logs that lower the barrier to entry, which has resulted in an oversupply of cheap but operationally constrained inventory that floods the market and depresses pricing. While average pricing has declined due to increased volume and automation, validated, high-privilege enterprise access (e.g., domain-level control) still commands premium pricing, indicating a bifurcated and still competitive market.”
| Month | Privately offered access (count) | YoY change (as stated) | MoM change |
| 2025-01 | 646 | +114% | – |
| 2025-02 | 614 | +117% | -32 |
| 2025-03 | 621 | +201% | +7 |
| 2025-04 | 739 | +278% | +118 |
| 2025-05 | 725 | +87% | -14 |
| 2025-06 | 1,127 | +154% | +402 |
| 2025-07 | 1,019 | +48% | -108 |
| 2025-08 | 860 | +41% | -159 |
| 2025-09 | 715 | +1% | -145 |
| 2025-10 | 706 | +37% | -9 |
| 2025-11 | 460 | -35% | -246 |
| 2025-12 | 641 | -76% | +181 |
| 2026-01 | 675 | +4% | +34 |
Growth in privately offered access YoY
Source: Darkweb IQ
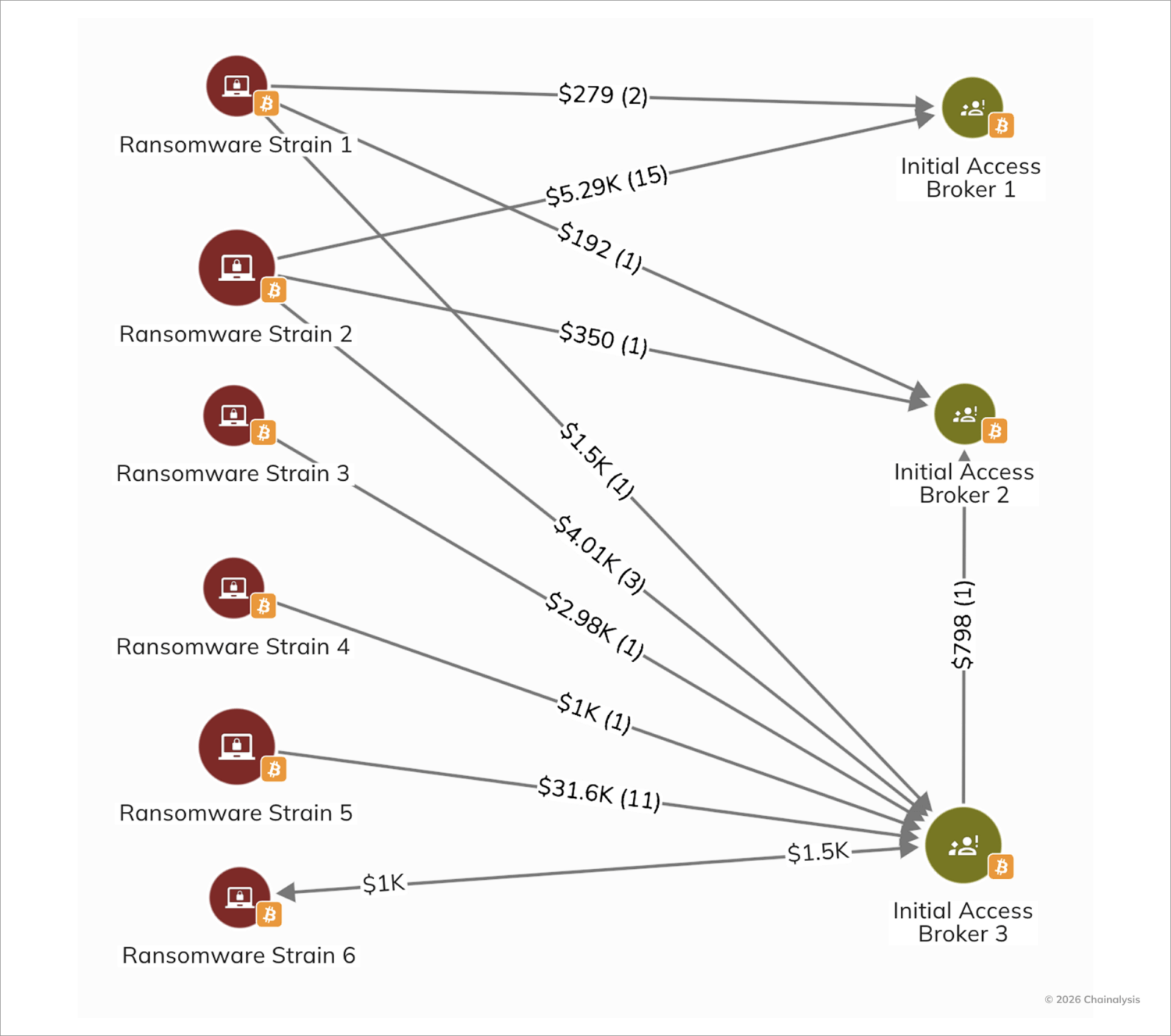
We can also visualize these trends on-chain, as shown in the Reactor graph below. This example illustrates both the varying prices of access being purchased by ransomware strains over time and the fact that IABs are also frequently purchasing access from other IABs.
Emerging tools and frameworks hint at a future where automation not only influences price, but also accelerates compromise and extortion cycles. For example, researchers documented ransomware groups experimenting with AI-driven negotiation interfaces in mid-2025, mirroring developments in the AI-enabled scam ecosystem.
Infrastructure enables both criminal syndicates and state-linked threat actors
Ransomware infrastructure — including bulletproof hosting and residential proxy networks, and malware loaders— is not used exclusively by financially motivated criminal syndicates nor exclusively used for criminal aims. The same service-based ecosystem also supports state-linked threat actors conducting espionage, influence operations, and financially motivated campaigns.
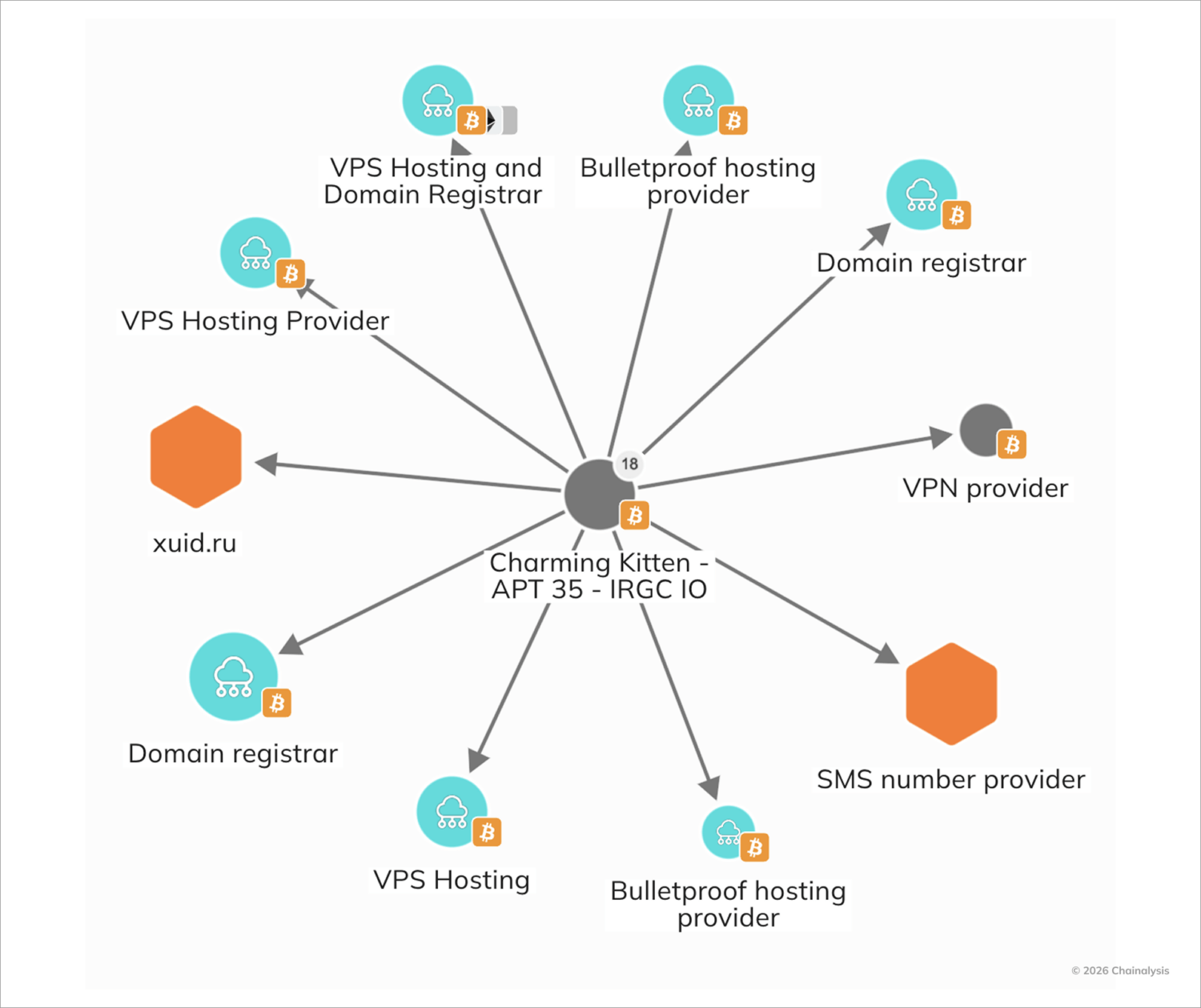
According to data leaked in 2025, Iran-linked cyber threat actors, including groups commonly tracked as Charming Kitten, the espionage and influence operations focused branch of Iran’s Islamic Revolutionary Guard Corps (IRGC) Intelligence Organization, continue to rely on commercially available hosting, proxy services, and compromised infrastructure to obscure attribution and blend into criminal traffic patterns. The increasing commoditization of access and anonymization services lowers the barrier between state and non-state cyber operations, allowing espionage campaigns to operate within the same technical substrate as ransomware affiliates.
This blurring of lines is not unique to Iranian operations, as Russia- and China-linked actors similarly exploit these infrastructure layers to support both financial crime and state-sponsored objectives.
- In 2025, authorities sanctioned Media Land, LLC, also known as Yalishanda, a Russia-based bulletproof hosting provider associated with cybercriminal services. Sanctions targeting infrastructure providers — rather than individual operators alone — reflect a growing recognition that hosting and routing layers are force multipliers for ransomware and state-backed campaigns alike.
- Microsoft’s disruption of the Russia-centric Lumma Stealer ecosystem further illustrates this convergence. While Lumma was widely used for credential theft in financially motivated campaigns, its infrastructure also enabled access brokering and downstream ransomware deployment. Targeting such tooling constrains both criminal monetization and state-aligned credential harvesting.
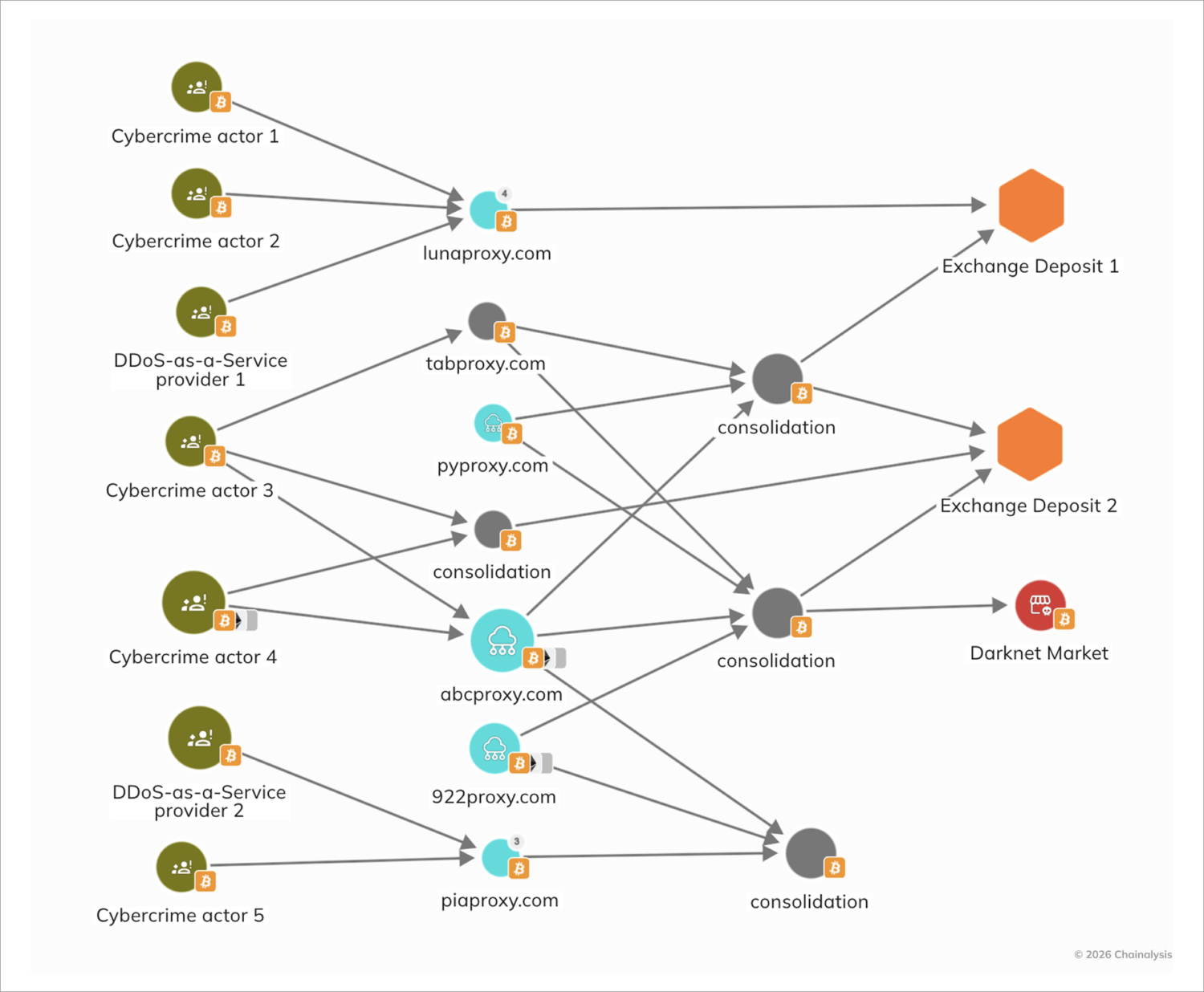
- As discussed in greater detail below, researchers also highlighted the role of Chinese proxy providers operating multiple residential proxy brands — including ABCProxy and 360Proxy — which offer large-scale IP rotation and anonymization services. These networks can be used to evade detection, conduct reconnaissance, and facilitate intrusion activity across both cybercrime and state-linked operations.
The overlap is significant: infrastructure providers can often advertise neutrality, serving any paying customer, although they may in some cases claim to ban CSAM. As a result, dismantling or sanctioning infrastructure nodes can generate cascading effects across ransomware affiliates, scammers, and state-aligned operators simultaneously.
This convergence reinforces a core dynamic of the modern cyber threat landscape: infrastructure is the strategic center of gravity. Disrupting it raises costs across the entire ecosystem — from extortion-driven syndicates to geopolitically motivated threat actors.
Public and private sectors making strides in disrupting ransomware’s enablement layers
In 2025, the fight against ransomware moved beyond targeting specific gangs to dismantling the shared services that power the broader cybercrime economy. “Loyalty and brand names matter less than access, tooling, and negotiation capability. For defenders and policymakers, this creates a moving target — disruption of one group no longer guarantees meaningful ecosystem-wide impact. Increasingly, the most effective pressure points appear to be upstream: initial access brokers and the shared tooling relied on across actors, as recent coordinated law enforcement operations have demonstrated,” says Camichel.
In May 2025, international authorities expanded Operation Endgame, a coordinated action involving Europol, the FBI, Germany’s BKA, the UK’s NCA, and other partners, targeting core malware loaders and ransomware infrastructure used by multiple criminal groups. The operation resulted in server seizures, arrests, and the disruption of several key malware families that functioned as entry points in some ransomware campaigns. These types of actions demonstrate that coordinated, cross-border disruption can materially degrade ransomware monetization pipelines while increasing operational friction and forcing actors to rebuild trusted tooling, hosting, and laundering relationships.
Beyond malware delivery systems, authorities also intensified pressure on the hosting environments that sustain these operations. Continued sanctions and indictments chipped away at bulletproof hosting providers (BPH) and laundering services, highlighting how these infrastructure components themselves have become targets for disruption and increasing risk for cybercriminals seeking to monetize extortion. For example, OFAC sanctions in July against AEZA Group, a BPH provider linked to high-volume abuse, demonstrated how crypto payments continue to flow through shielded infrastructure that facilitates ransomware and related attacks. Likewise, the sanctioning in February of Zservers, a provider associated with LockBit and other ransomware actors, underscored the degree to which infrastructure providers are embedded in ransomware monetization.
In parallel with sanctions and infrastructure seizures, the private sector in 2025 also drove significant disruptions of large-scale proxy services underpinning both ransomware and adjacent cybercrime activity. One notable case involved IPIDEA, a China-based residential proxy service advertising millions of proxy endpoints available for rent in any given week. Google’s blog on the takedown detailed how the service facilitated botnets including Aisuru and Kimwolf, and how its infrastructure was leveraged by threat actors engaged in espionage and information operations alongside financially-motivated campaigns. Google’s analysis found that several residential proxy brands shown below were controlled by the same actors behind IPIDEA reinforcing how a relatively small set of operators can service a wide range of illicit customers across the threat landscape.
On-chain data complement this technical analysis by revealing the financial interconnectedness of these services. Our analysis reveals shared consolidation wallets and deposit addresses at exchanges, suggesting overlapping ownership and coordinated fund flows. We also observed wallets connected with this network making deposits to a well-known cybercrime forum, and several proxy brands associated with this cluster maintained an advertising presence on multiple darknet markets, explicitly marketing services for anonymity and abuse.
Ultimately, this infrastructure-centric approach could change the economic calculus for attackers. While these disruptions have not translated into a drastic reduction in attack volume, they have imposed operational costs and increased friction for threat actors, who are facing coordinated pressure from governments and the private sector alike.
Contraction in revenue, but expansion in harm
The ransomware narrative of 2025 cannot be told through revenue figures alone. While payments declined modestly, the scale, sophistication, and strategic impact of attacks continued to expand. Organizations large and small — from global automakers to regional healthcare systems — faced extortion that disrupted operations, eroded trust, and faced systemic costs that far exceeded on-chain ransom totals.
In this context, the ransomware landscape in 2025 is best characterized by adaptation rather than retreat: extortion tactics continue to evolve, enabling actors to extract value and damage beyond traditional payment streams. For defenders and policymakers alike, this underscores a central truth of the modern ransomware era — effective response requires both robust defenses and strategic resilience to limit the total harm inflicted by these multifaceted threats.
This website contains links to third-party sites that are not under the control of Chainalysis, Inc. or its affiliates (collectively “Chainalysis”). Access to such information does not imply association with, endorsement of, approval of, or recommendation by Chainalysis of the site or its operators, and Chainalysis is not responsible for the products, services, or other content hosted therein.
This material is for informational purposes only, and is not intended to provide legal, tax, financial, or investment advice. Recipients should consult their own advisors before making these types of decisions. Chainalysis has no responsibility or liability for any decision made or any other acts or omissions in connection with Recipient’s use of this material.
Chainalysis does not guarantee or warrant the accuracy, completeness, timeliness, suitability or validity of the information in this report and will not be responsible for any claim attributable to errors, omissions, or other inaccuracies of any part of such material.