On Wednesday, July 15, Twitter accounts belonging to prominent individuals including Joe Biden, Barack Obama, Elon Musk, and many others were taken over by hackers who allegedly gained access to one of Twitter’s internal content moderation tools. Throughout the afternoon, they posted messages like the one screenshotted below, promising users that if they sent Bitcoin to the address given, they’d receive double that amount in return.

All in all, the scam took in 13.14 BTC worth approximately $120,000 USD over the course of the afternoon, though as we’ll explore, some of that total was likely contributed by the hackers themselves.
As soon as we saw reports of the hack unfolding on social media, we moved quickly to label the scammers’ collection addresses in our products so that law enforcement could more easily trace the funds and our cryptocurrency customers could block customers from sending funds to the scam and prevent the scammers themselves from cashing out. Blockchain analysis is critical here, and ultimately, we believe this case will be yet another example of how the visibility into fund movement enabled by cryptocurrencies like Bitcoin makes them a safer, more transparent asset than cash and other traditional forms of value transfer. Below, we’ll give you a breakdown of what happened during the Twitter hack and the current status of the funds.
Background information on cryptocurrency scams and trust trading
Unfortunately, cryptocurrency scams are nothing new. In fact, as we explored in our 2020 Crypto Crime Report, scams are by far the most prevalent category of cryptocurrency-related crime, accounting for 74% of all illicit transaction volume in 2019.
Cryptocurrency scams have continued to be a major issue in 2020.
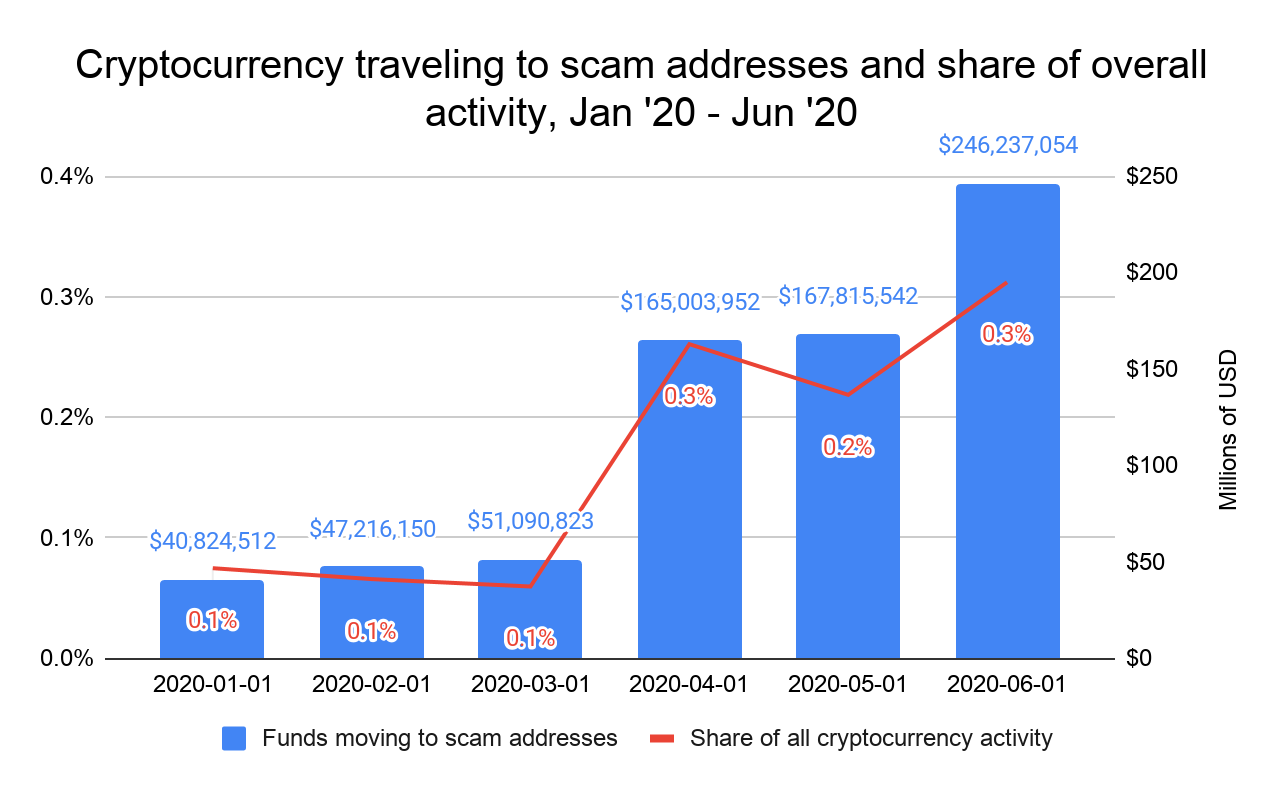
So far this year, scams have taken in more than $381 million from victims. This would put 2020 cryptocurrency scam revenue well below the pace it was on in 2019, largely due to the absence of a major Ponzi scheme like last year’s PlusToken, but still makes scams the largest category of cryptocurrency-related crime so far this year. The scam revenue figure for the first half of 2020 may also grow later as we learn of currently unreported scams, attribute their cryptocurrency addresses, and incorporate their activity into this data.
We also have to note that the scam perpetrated by the Twitter hackers isn’t new either. “Trust trading” scams, in which the scammer impersonates a notable person or company on social media and implores users to send them cryptocurrency in return for more later, have been going on for years.
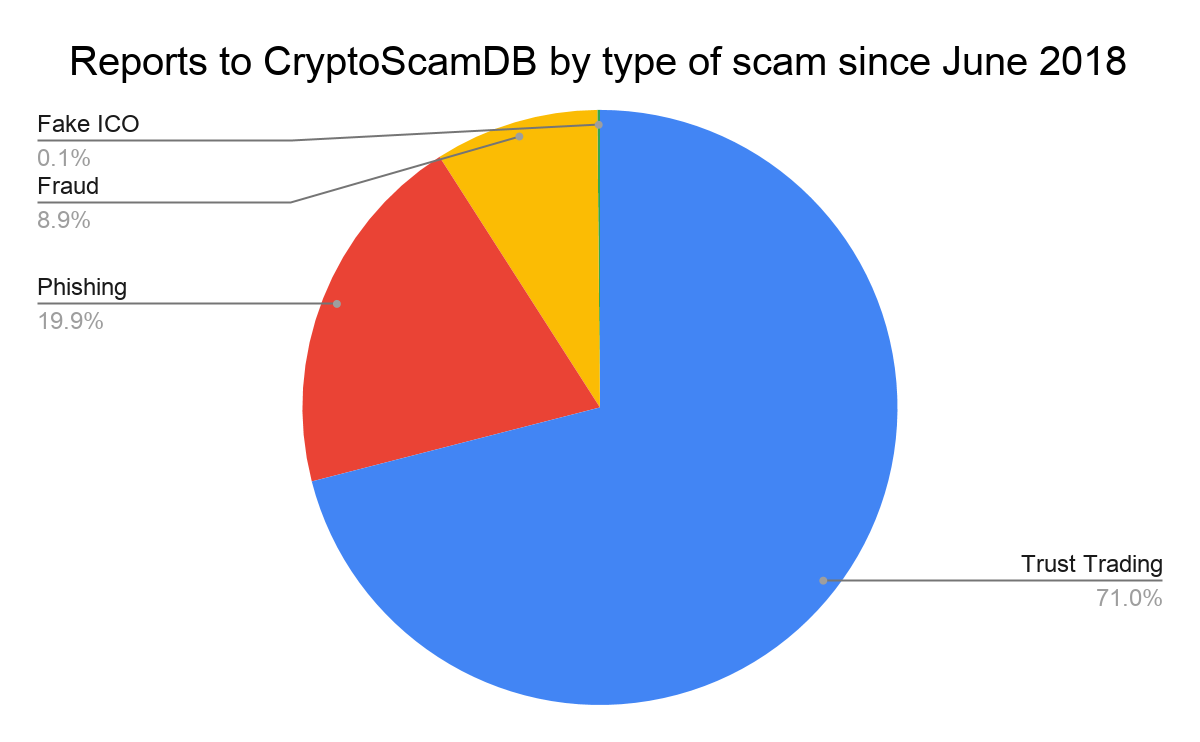
In fact, according to CryptoScamDB, an open source database where users can report scams and their associated cryptocurrency addresses, trust trading is the most frequently reported type of scam by a wide margin. Of course, what separates the Twitter hack from most trust trading scams is that the cybercriminals actually managed to broadcast their messages from the actual accounts of the celebrities they impersonated rather than create fake accounts.
The breakdown: What happened July 15 and where the stolen funds are now
The attack began at 2:16 PM when hackers took over the account of a cryptocurrency trader and influencer known as AngeloBTC and began soliciting payments via Twitter direct messages to join a made up Telegram group devoted to Angelo’s trading tips. Over the next four hours, the hackers took over the accounts of several other celebrities and influencers — at first just those in the cryptocurrency world but soon general celebrities as well — and began publicly tweeting out messages soliciting payments to the Bitcoin addresses under their control.
The messages posted from the hacked accounts included one of three Bitcoin addresses to which victims were asked to send funds:
- bc1qxy2kgdygjrsqtzq2n0yrf2493p83kkfjhx0wlh (this is the primary donation address that was included in the majority of posts)
- bc1q0kznuxzk6d82e27p7gplwl68zkv40swyy4d24x
- bc1qwr30ddc04zqp878c0evdrqfx564mmf0dy2w39l
All in all, those three addresses received 13.14 BTC (worth approximately $120,000) over the course of the day. However, not all of those funds came from victims. Approximately $20,000 of that total came from a suspicious address that we believe belongs to the hackers themselves. This is a common technique scammers use to make it appear more people have sent money to the scam and build trust with potential victims who examine the scam address using a blockchain explorer.
From there, most of the stolen funds were consolidated in the Bitcoin wallet address 1Ai52Uw6usjhpcDrwSmkUvjuqLpcznUuyF, which we’ll refer to as the scam cashout address. The scam cashout address has been active since May 3, 2020 and has interacted with several cryptocurrency services. Notably, this address received an additional 7.88 BTC (approximately $66,000 USD) on July 15, though it was never broadcast on Twitter.
Of the approximately 21 BTC deposited to the scam cashout address over the lifetime of that wallet, as of 4:30 PM ET July 22, 2020, roughly 9 BTC is sitting in 23 wallets, 8 BTC has been sent to mixing services like Wasabi Wallet, and 4 BTC has been sent to other entities. As this is an ongoing investigation, we cannot disclose any additional information on the services that have received funds.
7/23/20 UPDATE: The scammers have moved the funds since the paragraph above was published. As of July 23, 2020 at 1:00 PM ET, roughly 5.5 BTC is sitting in 23 wallets controlled by the hackers, 10 BTC total has been sent to mixing services, and 5.5 BTC total has been sent to other entities.
Nathaniel Popper of the New York Times spoke with two of purportedly three individuals behind the Twitter hack. The two individuals indicated that all three hackers met in a Discord chat server devoted to taking over so-called “OG accounts” of various social media platforms associated with one-letter account names that are typically claimed early in the lifespan of a given social media platform — in the case of Twitter, this would mean accounts such as “@G” and the like. Those individuals indicated that the third as yet uncontacted member of the group was the driving force behind the hack, and the one who initially gained access to the internal Twitter content moderation tool used to take over the accounts.
We will continue to share updates on this case as appropriate.



