Qubit was a South Korea-based DeFi lending protocol built on the BNB chain. Qubit also ran an associated protocol, the QBridge, that allows users to use assets on other chains as collateral to borrow against on Qubit, without actually moving those other assets onto BNB Chain. Users send assets they want to collateralize to a QBridge smart contract on those assets’ chains, and QBridge mints an equivalent asset on the BNB Chain.
Unfortunately, as has happened with many cross-chain bridges, hackers found an exploitable error in the code governing QBridge, and were able to drain the protocol of all of its holdings — roughly $80 million in assets, making it South Korea’s largest crypto theft of 2022. We can now share publicly for the first time our assessment that this hack was likely the work of North Korea-linked hackers, as was the case with so many other large DeFi hacks in 2022. Let’s take a look at how the Qubit hack unfolded.
How Qubit was hacked
The exploit the Qubit hackers discovered allowed them to mint unlimited qXETH — an asset meant to represent Ether bridged from the Ethereum blockchain — from the QBridge, without actually depositing any Ether. The hackers used the unbacked qXETH as collateral to “borrow” all of the assets held by the protocol — mostly BNB coin but also several BEP-20 tokens — worth roughly $80 million at the time of the theft. The hackers then bridged those funds to the Ethereum blockchain.
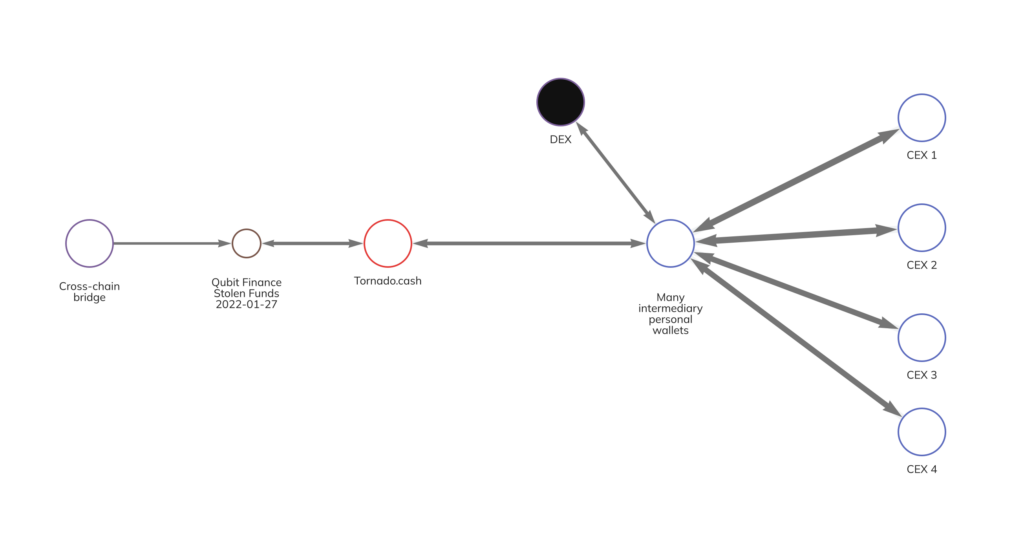
Once they bridged the funds from BNB Chain to Ethereum, the hackers used what was at the time North Korean crypto criminals’ go-to money laundering strategy: They sent the funds to the crypto mixer Tornado Cash. We can see an example of some of that activity following the Qubit hack below:
The hackers received their newly mixed Ether from Tornado Cash, and from there sent a portion to a decentralized exchange to be swapped for different ERC-20 tokens, while the rest was moved to deposit addresses at various centralized crypto exchanges. The Qubit hack exemplifies many of the key elements of the North Korean hacking strategy we saw in 2022: Exploit a DeFi protocol, bridge the funds to a blockchain where funds can’t be frozen, mix them, and move them to a centralized exchange. In this case, South Korea’s Transnational Crime Information Center (TCIC) and NIS (National Intelligence Service) were able to trace the funds in partnership with Chainalysis following the theft.
Fighting the North Korean crypto hacking threat
While North Korea-linked hackers are undoubtedly sophisticated and represent a significant threat to the cryptocurrency ecosystem, law enforcement and national security agencies’ ability to fight back is growing. Last year, for example, we saw the first ever seizure of funds stolen by North Korea-linked hackers, when agents recovered $30 million worth of cryptocurrency stolen in the Axie Infinity Ronin Bridge hack. We expect more such stories in the coming years, largely due to the transparency of the blockchain. When every transaction is recorded in a public ledger, it means that law enforcement always has a trail to follow, even years after the fact, which is invaluable as investigative techniques improve over time. Their growing capabilities, combined with the efforts of agencies like OFAC to cut off hackers’ preferred money laundering services from the rest of the crypto ecosystem, means that these hacks will get harder and less fruitful with each passing year.
This material is for informational purposes only, and is not intended to provide legal, tax, financial, or investment advice. Recipients should consult their own advisors before making these types of decisions. Chainalysis has no responsibility or liability for any decision made or any other acts or omissions in connection with Recipient’s use of this material.
Chainalysis does not guarantee or warrant the accuracy, completeness, timeliness, suitability or validity of the information in this report and will not be responsible for any claim attributable to errors, omissions, or other inaccuracies of any part of such material.