Cryptocurrency mining is a crucial part of our industry, but it also holds special appeal to bad actors, as it provides a means to acquire money with a totally clean on-chain original source. We’ve discussed in the past how because of these characteristics, heavily sanctioned nation states like Iran have turned to cryptocurrency mining to build capital without going through the traditional financial system. More recently, cybersecurity firm Mandiant published research on how North Korean hacking syndicate Lazarus Group is using stolen cryptocurrency to acquire freshly mined crypto via hashing services.
However, nation state actors aren’t the only ones using crypto mining to enhance their money laundering capabilities. Chainalysis has discovered examples of what appear to be conventional crypto criminals doing the same thing. Below, we’ll look at examples of ransomware actors and crypto scammers who appear to be using mining pools for money laundering, and estimate this activity at scale.
Example 1: Ransomware funds and mining proceeds co-mingle at high-balance exchange deposit address
Our first example concerns a highly active deposit address at a mainstream exchange that has received substantial funds from both mining pools and wallets associated with ransomware.
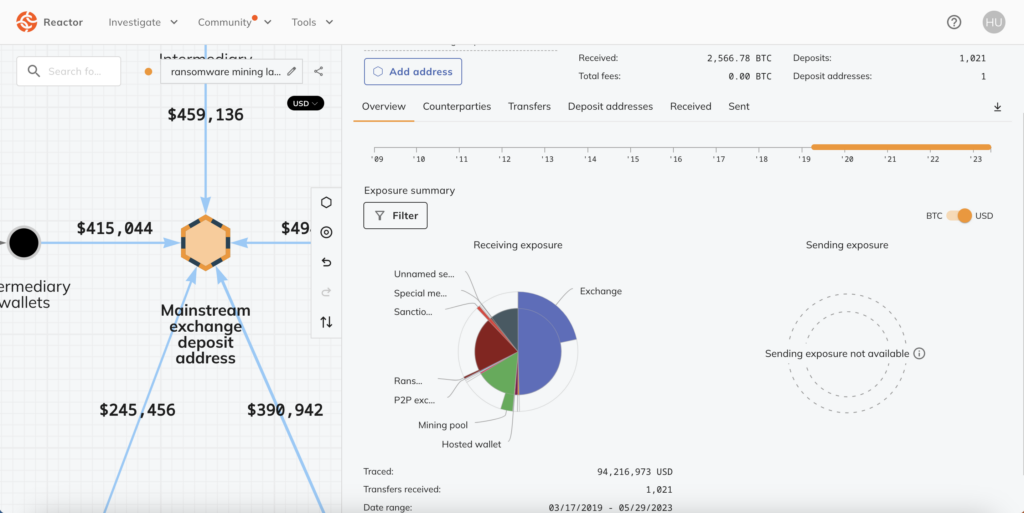
Of the $94.2 million worth of cryptocurrency ever sent to this deposit address, $19.1 million has come from ransomware addresses and $14.1 million has come from mining pools. We can see some of this activity on the Chainalysis Reactor graph below.
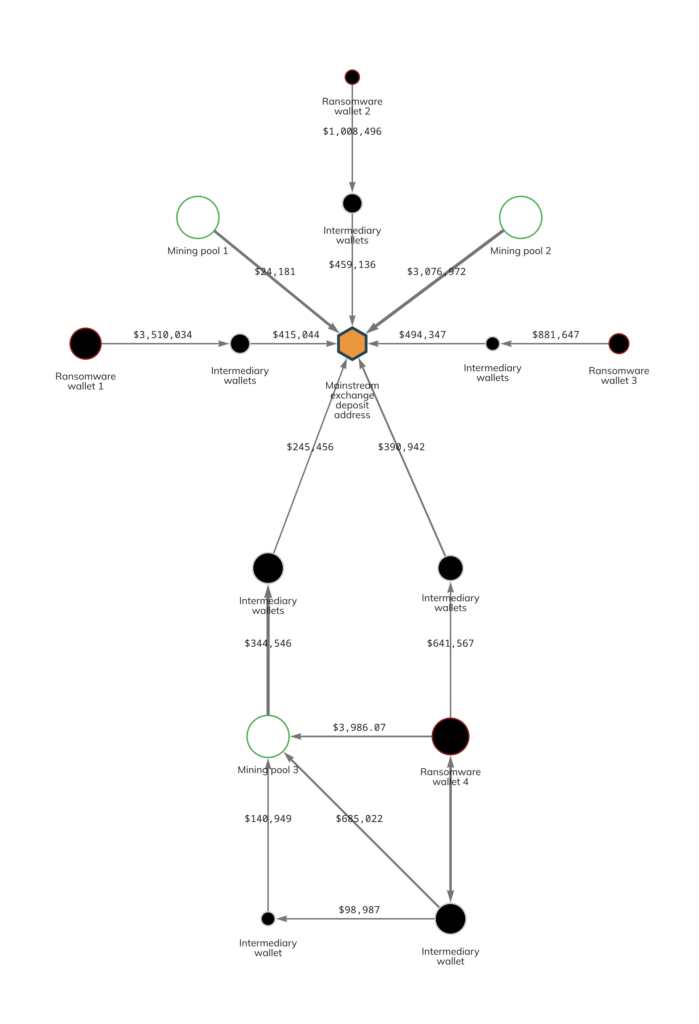
In many cases, we see ransomware actors sending to the deposit address through intermediary wallets. However, the interplay between Ransomware wallet 4 and Mining pool 3 at the bottom of the graph is especially interesting. Both the ransomware wallet and the mining pool have sent substantial amounts to the exchange deposit address via intermediaries. But we also see that in some cases, the ransomware wallet has sent funds to the mining pool, both directly and via intermediaries. This may represent a sophisticated attempt at money laundering, in which the ransomware actor funnels funds to its preferred exchange via the mining pool in order to avoid triggering compliance alarms at the exchange. In this scenario, the mining pool acts similarly to a mixer in that it obfuscates the origin of funds (reminder: you can’t trace crypto through services, mining pools included) and creates the illusion that the funds are proceeds from mining rather than from ransomware.
Our data suggests that this abuse of mining pools by ransomware actors may be rising. Since the start of 2018, we’ve seen a large, steady increase in value sent from ransomware wallets to mining pools.
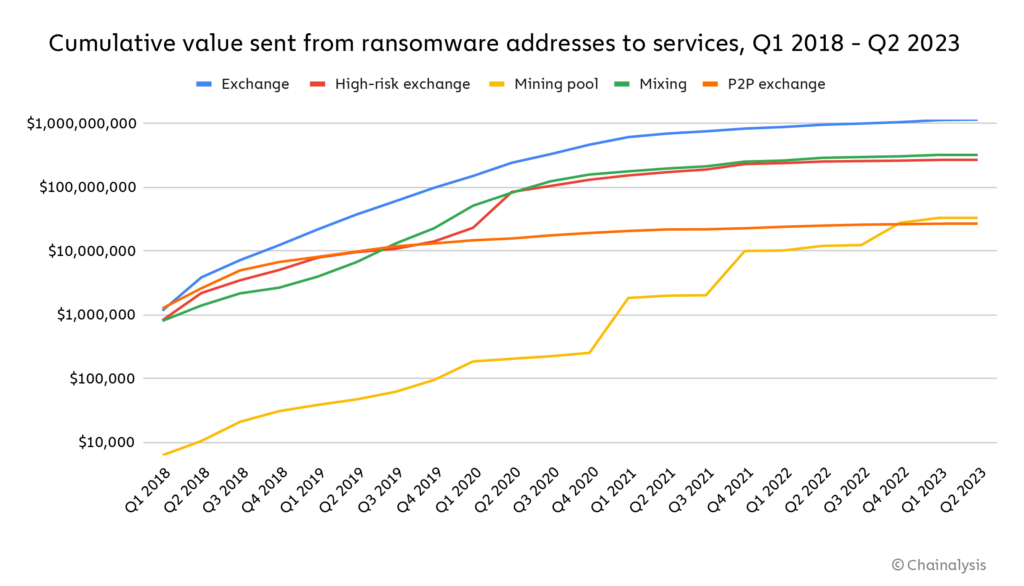
That increase could indicate that more ransomware actors are funneling funds to exchanges via mining pools.
More generally, we also see lots of cryptocurrency moving from ransomware wallets to exchange deposit addresses that receive significant funds from mining pools. While this activity should be easier for exchanges to catch, it’s possible that in cases like these, ransomware actors are trying to pass off their own funds as mining proceeds, even though they’re not first moving the funds through a mining pool. In total, 372 exchange deposit addresses have received at least $1 million worth of cryptocurrency from mining pools and any amount from ransomware addresses. The chart below shows how much those deposit addresses have received from ransomware addresses since January 2018.
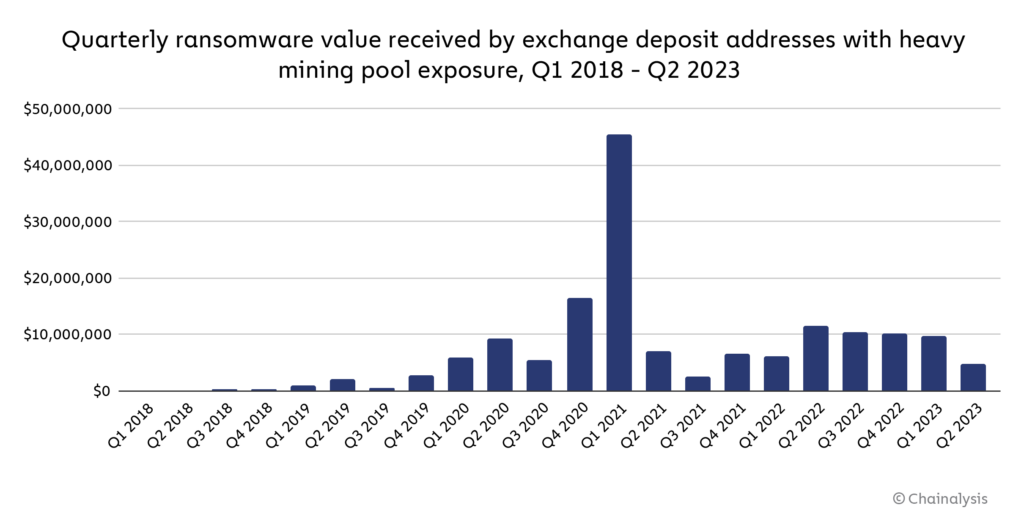
These exchange deposit addresses have received $158.3 million from ransomware addresses since the start of 2018, which is a significant share of the total value sent to exchanges by all ransomware addresses during the time period studied — and keep in mind, this figure is likely an underestimate, and will grow as we identify more ransomware addresses involved in this activity. Overall, the data suggests that mining pools may play a key role in many ransomware actors’ money laundering strategy.
Example 2: Money launderer mingles Bitcoin from scams with mining proceeds
The second example concerns two wallets associated with money launderers who have moved millions of dollars’ worth of Bitcoin associated with a notorious scam, BitClub Network, to mainstream exchanges. BitClub Network bilked investors out of hundreds of millions of dollars between 2014 and 2019 with false promises of Bitcoin mining operations that would pay out enormous returns, until its administrators were indicted by the U.S. Department of Justice.
Earlier in 2019 and prior to that indictment, BitClub Network moved millions of dollars’ worth of Bitcoin to wallets associated with underground money laundering services we believe to be based in Russia. Over the next three years, those money laundering wallets moved Bitcoin to deposit addresses at two mainstream exchanges. Within that time period — specifically, between October 2021 and August 2022 — a Russia-based Bitcoin mining operation also moved millions of dollars’ worth of Bitcoin to the same sets of deposit addresses at both exchanges. We can see this activity on the Reactor graph below.
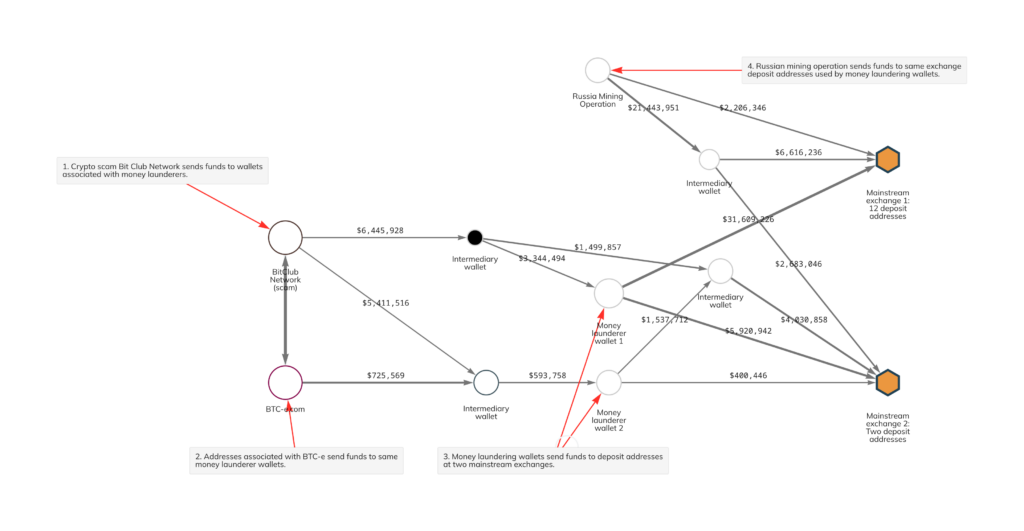
Interestingly, one of the money laundering wallets also received funds from BTC-e, which were also funneled to the same deposit addresses used to launder BitClub Network funds between March 2017 and November 2018. BTC-e and BitClub also sent funds to one another back in 2017. BTC-e was a Russia-based exchange shut down in 2017 for facilitation of money laundering, including the laundering of funds stolen in the infamous Mt. Gox hack.
We believe it’s possible that the money launderers in this case purposely mingled funds from BitClub and BTC-e with those gained from mining in order to make it look like all of the funds sent to the two exchanges came from mining, like in our last example.
As is the case with ransomware, the data suggests other crypto scammers and money launderers working on their behalf are also using mining pools as part of their money laundering process. Let’s look at all value received since 2018 by exchange deposit addresses with scam exposure that have also received at least $1 million worth of cryptocurrency from mining pools.
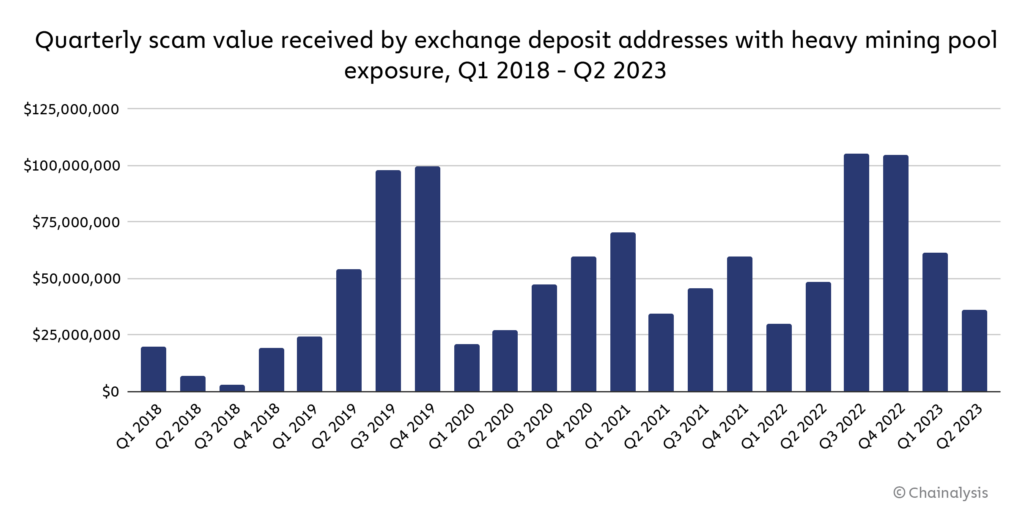
In total, deposit addresses fitting that profile have received just under $1.1 billion worth of cryptocurrency from scam-related addresses since 2018.
Better compliance can solve this problem
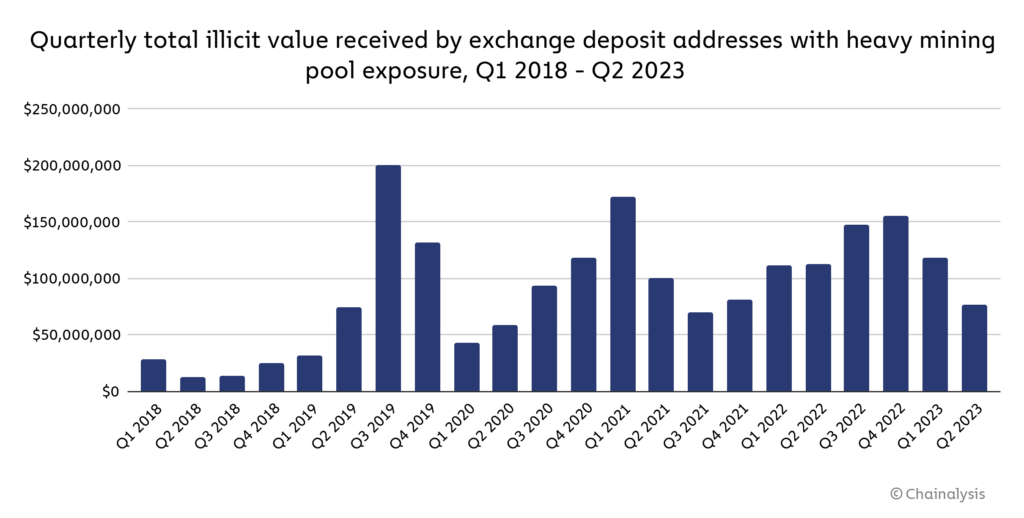
The examples we share above show that some mining operations and pools can be exploited by crypto criminals for money laundering purposes, specifically those with operations that expand beyond just mining to include services typically offered by VASPs. In fact, if we take the same methodology we used to identify ransomware and scamming money laundering via mining at scale, and apply it to all types of crypto crime, we find that nearly $1.8 billion in illicit cryptocurrency has moved to deposit addresses with heavy mining exposure.
However, this is a solvable problem. The first and most important fix would be for mining pools and hashing services to enact more strenuous wallet screening measures in addition to KYC, using blockchain analysis to check users’ origins of funds and reject crypto coming from illicit addresses. Secondly, exchanges should be careful to consider the full exposure profile of any wallets sending funds to them — with tools like Chainalysis KYT, it isn’t possible for crypto received from illicit addresses to “hide” alongside crypto obtained via mining, as we saw primarily in our second example. By taking steps like those, we can deny bad actors access to a potentially valuable money laundering capability, and ensure that mining, which is a core functionality of Bitcoin and many other blockchains, isn’t compromised.
This material is for informational purposes only, and is not intended to provide legal, tax, financial, or investment advice. Recipients should consult their own advisors before making these types of decisions. Chainalysis has no responsibility or liability for any decision made or any other acts or omissions in connection with Recipient’s use of this material.
Chainalysis does not guarantee or warrant the accuracy, completeness, timeliness, suitability or validity of the information in this report and will not be responsible for any claim attributable to errors, omissions, or other inaccuracies of any part of such material.